Cross-Mapping Policies: Build Once, Comply Everywhere
Unify controls, map overlapping requirements, centralize evidence, and use AI to automate cross-framework compliance for continuous, audit-ready security.

Organizations often waste time and resources duplicating efforts to follow best practices for multi-framework compliance like ISO 27001, SOC 2, NIST 800-53, and HIPAA. These frameworks share up to 96% of their core controls, yet compliance teams frequently redo similar tasks. Cross-mapping policies solve this problem by consolidating overlapping requirements into a single, reusable system. This approach:
- Reduces redundant work by up to 60%.
- Cuts compliance costs by 20–30%.
- Boosts control maturity by 40%.
For example, one multi-factor authentication (MFA) policy can simultaneously satisfy requirements across frameworks, streamlining audits and evidence collection. Automated tools like ISMS Copilot further simplify this process by using AI to map controls across frameworks in minutes, saving hundreds of hours of manual work. By centralizing evidence and automating updates, organizations can maintain continuous compliance and reduce audit preparation time by up to 90%.
This article explains how to implement cross-mapping policies effectively, from building a unified control library to leveraging AI-powered tools for automation. The goal? Simplify compliance, reduce costs, and focus on mitigating real risks.
Mapping Across an Ocean of Security Frameworks, Part 1 - Thomas Sager, Tony Sager - SCW 92
sbb-itb-4566332
1. Build a Unified Control Library
A unified control library brings together compliance requirements into a single, reusable system. Instead of crafting separate policies for frameworks like SOC 2, ISO 27001, and NIST 800-53, you can define one internal control and map it to all relevant standards. For example, a single multi-factor authentication (MFA) policy can simultaneously address FedRAMP IA-2, CMMC IA.2.078, SOC 2 CC6.3, and ISO 27001 A.9.4.2.
To get started, select a foundational baseline. Frameworks like NIST 800-53 or ISO 27001 are modular and already align with many others, making future mappings more straightforward. This step ensures consistency and simplifies the process. Using an AI implementation assistant can further accelerate these foundational steps. For instance, the Open Security Architecture library includes 8,604 mappings between NIST 800-53 and 21 other major frameworks. Next, develop modular controls. Each control should have a unique ID, a clear statement, mapped citations, assigned owners, and specific evidence requirements.
Reusability Across Frameworks
When you collect evidence for one control - such as MFA configuration logs - it can satisfy multiple framework requirements at once. This reduces redundant data collection and can cut audit preparation time by as much as 82%. Adding a new framework later becomes easier, as you only need a "delta" analysis to identify any unique requirements not already covered.
Automation and Scalability
Reusability becomes even more powerful when paired with automation. Storing your control library in a structured system - like a GRC platform, version-controlled repository, or machine-readable formats like YAML or JSON - enables automated checks, live dashboards, and real-time alerts. Organizations that implement a common control framework often see a 20% to 30% reduction in the time spent identifying controls for industry-specific regulations.
"Unified control mapping turns scattered frameworks into a single, reusable system of record." – Continuum GRC
Alignment with Risk Management
Connect your control library to a central risk register and asset inventory. This ensures that controls address actual organizational risks. Companies using integrated benchmarks report a 40% improvement in control maturity. Focus on mapping controls by their security objective and intent, rather than relying solely on keywords. This approach minimizes compliance gaps and ensures that auditors accept shared evidence. It aligns perfectly with the "build once, comply everywhere" principle by standardizing policies across frameworks.
Ease of Audit Preparation
A unified control library simplifies audit preparation by consolidating evidence into a single, accessible repository. Auditors can review one evidence package - such as an MFA configuration report - to satisfy requirements for SOC 2, ISO 27001, and NIST simultaneously. Sharing your mapping logic with auditors or third-party assessors before the audit ensures smoother acceptance of your evidence. This approach eliminates the need to sift through siloed programs, making the entire process more efficient.
2. Identify Overlapping Requirements Manually
The first step in achieving unified compliance is to manually map out the overlapping requirements across different frameworks. This process helps establish a clear foundation by pinpointing shared controls. Start by identifying the regulations relevant to your industry, location, and business model. For instance, a financial services firm might need to comply with DORA, whereas a payment processor would need to address PCI DSS requirements. Once you’ve determined your obligations, select a foundational framework - like NIST 800-53 or ISO 27001 - to act as your internal benchmark. This framework will serve as your "source of truth" for aligning with other standards. From there, create a detailed matrix to outline how controls relate to one another.
One valuable tool for this process is a crosswalk document. This matrix lists control IDs, descriptions, and their mapped relationships across frameworks. The focus should be on mapping controls based on their underlying security goals and purpose, rather than simply matching keywords. For example, NIST's "Account Management" (AC-02) can align with ISO 27001's A.5.15, PCI DSS 7.2.1–7.2.6, and DORA Article 94 because they all aim to achieve the same objective. Interestingly, a well-developed NIST 800-53 baseline can cover around 78% of NIS2 requirements.
"A security architect who can show that AC-02 (Account Management) simultaneously satisfies ISO 27001 A.5.15, PCI DSS 7.2.1–7.2.6, and DORA Art.94 reduces evidence preparation from weeks to days." – Chris Lethaby, Co-founder, Open Security Architecture
When creating your mappings, note any nuances and confidence levels for each control. Some controls may only partially overlap; for instance, one framework might require quarterly reviews, while another demands continuous monitoring. Once the mapping is complete, conduct a gap analysis to identify any requirements from secondary frameworks that your chosen baseline doesn’t fully address, such as specific reporting timelines for certain jurisdictions. Afterward, validate your mappings with stakeholders - including risk managers, compliance officers, and engineering teams - to ensure accuracy before audits begin.
One major challenge with manual mapping is keeping the process sustainable. Spreadsheets, while helpful initially, can quickly become outdated as frameworks evolve, like with PCI DSS 4.0 or FedRAMP Revision 5. While manual mapping provides clarity on control intent, its static nature often leads organizations to explore automated solutions for long-term efficiency. Using a cross-framework ISMS assistant can bridge these gaps by dynamically mapping controls as requirements change.
3. Use AI-Powered Automated Mapping with ISMS Copilot
While manual mapping strategies have their place, relying on spreadsheets to track compliance across 20+ frameworks quickly becomes unmanageable as regulations evolve. That’s where AI automation steps in to simplify the process. ISMS Copilot leverages Retrieval-Augmented Generation (RAG) to draw from a specialized dataset built on hundreds of consulting projects. This enables precise control mappings across standards like ISO 27001, SOC 2, NIST 800-53, DORA, NIS2, and other supported frameworks. The result? What once took months can now be accomplished in days, offering a more streamlined approach to compliance.
Reusability Across Frameworks
One of the standout features of ISMS Copilot is its ability to create a unified control library. Here’s how it works: a single control - say, Access Management - can automatically map to multiple standards at once. For instance, a Password Policy might satisfy ISO 27001 Annex A, SOC 2 CC6.2, and NIST CSF requirements simultaneously. A real-world example? A cloud analytics company operating in the finance and healthcare sectors reused 75% of their ISO 27001 controls for SOC 2 compliance. This approach allowed them to complete audits for ISO 27001, SOC 2 Type II, and NIST CSF in under eight months - less than half the 18 months typically needed with traditional consulting. The payoff? They secured $10 million in new enterprise deals.
Automation and Scalability
Mapping frameworks manually is no small task. For just two frameworks with 100 requirements each, experts can spend 300–500 hours on the process. ISMS Copilot eliminates much of this workload through automated gap analysis. For example, when adopting a new framework, the system identifies overlaps - such as discovering that 80% of SOC 2 requirements are already covered by existing ISO 27001 controls. This approach highlights only the new or "delta" requirements, saving time without sacrificing accuracy.
Efficiency aside, aligning controls with risk management is just as critical.
Alignment with Risk Management
Unlike general-purpose AI tools like ChatGPT or Claude, ISMS Copilot is built specifically for compliance. Its "brain" doesn’t pull from the vast internet but instead relies on a proprietary library of compliance expertise. Tristan Roth, Founder & CEO of Better ISMS, puts it best:
"Our AI doesn't search the whole internet. It only uses our own library of real-world compliance knowledge. When you ask a question, you get a straight, reliable answer".
This focus ensures that the platform provides practical, field-tested guidance for implementing controls tailored to specific organizational risks, even for complex regulations like the EU AI Act.
Ease of Audit Preparation
Preparing for audits has never been simpler. ISMS Copilot generates auditor-ready documentation in minutes, with outputs structured to meet exact expectations. Evidence items, such as MFA logs, are tagged once and automatically applied across all relevant frameworks, eliminating repetitive tasks like duplicate uploads. The platform’s "Workspaces" feature helps keep audits and client projects neatly separated, ensuring policies, evidence, and instructions remain organized and distinct.
Interested in trying it out? Start with a free trial at chat.ismscopilot.com. Subscriptions start at $24/month for individuals and $250/month for teams.
4. Centralize Evidence and Ownership
Managing scattered spreadsheets and unorganized folders can waste countless hours as teams scramble to locate the right audit evidence. A centralized repository eliminates this inefficiency by creating a single, reliable location for all controls, artifacts, and mappings. This approach not only simplifies document retrieval but also enables efficient tagging and clear ownership assignment.
Each piece of evidence should be tagged with essential details like its source, timestamp, mapped controls, review frequency, and retention period. For instance, tagging MFA logs once could simultaneously satisfy requirements for SOC 2 CC6.1, ISO 27001 A.9.2.3, and HIPAA 164.308(a). By centralizing and tagging evidence this way, organizations can reuse it for 80–90% of overlapping controls across frameworks, reducing audit preparation time by as much as 82%.
Assigning clear ownership for evidence is equally important. Instead of assigning responsibility for entire frameworks, designate specific stakeholders for individual controls. For example, an IAM lead might handle access controls, HR could manage onboarding documentation, and Security Engineering might oversee encryption attestations. This targeted approach prevents last-minute panic and reduces burnout.
"Someone should be responsible for uploading the right artifact, checking that it's current, and verifying that it meets the auditor's expectations." - Emily Bonnie, Senior Content Marketing Manager, Secureframe
To maintain accountability, set service-level agreements (SLAs) for control owners, requiring tasks like evidence reviews or attestations to be completed within five business days. Automate reminders for upcoming reviews of risks, policies, or controls. For critical areas like privileged access changes, introduce a two-person approval process to ensure thorough oversight. This tiered approach automates routine tasks, such as encryption status checks, while reserving human attention for controls with higher security implications. For more complex requirements, an AI designed for detailed compliance tasks can manage multi-step evidence workflows.
5. Implement Continuous Monitoring and Updates
Compliance isn’t a one-and-done task. Regulations change, frameworks evolve, and your technology stack won’t stay static forever. In fact, 65% of organizations say that keeping up with the rapid pace of regulatory changes makes it harder to maintain compliance with information security best practices. Without a system for continuous monitoring, you could find yourself scrambling to gather evidence and update policies just before audits. That’s where automated, real-time solutions come into play.
Modern AI compliance assistants can monitor global regulatory bodies in real time, alerting you to updates in frameworks like ISO 27001, SOC 2, or GDPR. These systems identify which internal policies and controls are affected by the changes. For example, if PCI DSS introduces new testing requirements, the system flags the gaps and immediately suggests updated controls. While manual scoping might take 40+ hours, automated mapping can reduce that effort to mere minutes.
By integrating your GRC platform with your tech stack - including cloud providers, HR systems, identity management tools, and ticketing systems - you can enable real-time evidence collection. This evidence is securely logged and timestamped continuously. If a control fails or a review task is overdue, the system sends instant alerts to the responsible team member. This level of automation can slash audit preparation time by up to 90%, cutting it from 80–120 hours to under 10.
Another major advantage is cross-mapped controls. A single policy update, such as changing password complexity requirements, can automatically sync across multiple frameworks like NIST, ISO 27001, and SOC 2. This eliminates the need for manual updates and ensures that your compliance stays consistent across all frameworks. Automated monitoring can boost operational efficiency by 40%, freeing your team to focus on higher-value tasks like strategic risk management.
"A unified system isn't just a present-day fix; it's a future safeguard." - Christie Rae, Content Marketing Specialist, ISMS.online
To further streamline compliance, establish a centralized risk register that maps risks to multiple frameworks. Provide auditors with read-only access to a portal where they can view real-time, validated evidence. This approach aligns with the "build once, comply everywhere" strategy, keeping your compliance program in a live, audit-ready state. With continuous visibility into your security posture, you’ll be better equipped to adapt to changes and maintain a strong compliance foundation.
6. Integrate with GRC Platforms for Scalability
Connecting your cross-mapped policies to a GRC (Governance, Risk, and Compliance) platform can make scaling compliance much simpler. These platforms act as a single system of record, where one internal control - like your multi-factor authentication policy - automatically links to frameworks such as SOC 2 CC6.3, ISO 27001 A.9.4.2, and NIST 800-53 IA-2. Essentially, you create the control once, and the platform manages the documentation across all frameworks for you. This not only streamlines documentation but also boosts efficiency across compliance operations.
One of the key benefits is evidence reusability. Evidence collected once can be applied across multiple frameworks automatically. APIs play a big role here by pulling and timestamping evidence directly from cloud providers, identity systems, and ticketing tools. This automation can cut down manual compliance work by up to 80%, allowing your team to focus on higher-value tasks instead of spending time compiling evidence.
"Unified control mapping identifies overlaps across frameworks and builds a single control library that satisfies multiple frameworks simultaneously." - Continuum GRC
GRC platforms also simplify policy management through cascading updates. For example, if you update your password policy in the central control library, that update automatically syncs across all linked frameworks. This eliminates the need for repetitive updates across different documents, aligning with the "build once, comply everywhere" approach. By automating policy propagation, organizations often see a 20% to 30% reduction in compliance costs, while integrated mapping strategies can improve control maturity by 40%.
When it comes to audits, GRC platforms provide auditor portals with read-only access to validated, audit-ready evidence bundles. These portals, along with centralized control libraries, ensure continuous readiness. Instead of rushing to gather documents right before an audit, auditors can access real-time dashboards that show your compliance status across all frameworks. This shifts audits from a reactive, last-minute scramble to a proactive, ongoing process. It also gives your organization the flexibility to pursue new certifications without having to start from scratch each time.
7. Streamline Audit Preparation
Effective audit preparation builds on unified control libraries and centralized evidence management, creating a stronger compliance foundation. By cross-mapping policies, organizations can maintain ongoing audit readiness. For instance, mapping a single internal control - like periodic access reviews - to multiple framework citations (e.g., SOC 2 CC6.1, ISO 27001 A.9.2.5, HIPAA 164.308(a), and PCI DSS 7.2.5) allows one evidence package to satisfy multiple audit requirements at once. This approach can help organizations reuse evidence for 80–90% of overlapping controls across major frameworks, cutting down on redundant data collection.
Reusability Across Frameworks
A unified control library connects one control statement to multiple regulatory citations, ensuring traceability from written policies to implemented procedures and verifiable evidence. Metadata tagging takes this a step further, enabling precise filtering and quick generation of targeted evidence packages. For example, during ISO 27001 recertification, you can pull all relevant evidence tagged to ISO controls - even if it was originally gathered for a SOC 2 audit. This unified system simplifies preparation and supports automated, scalable audit processes.
Automation and Scalability
Automation tools integrate with platforms like AWS, Okta, and Jira to update evidence in real time. A great example of this is Arbor Education, which reduced its audit preparation cycle by over 66% - shrinking it from six weeks to just two - by centralizing control mapping and automating evidence collection for ISO 27001, ISO 9001, PCI DSS, and GDPR. This shift from reactive, last-minute efforts to proactive preparation allows auditors to access real-time compliance dashboards, eliminating the need for teams to scramble and compile documents under pressure.
Alignment with Risk Management
When cross-mapped policies are tied to your risk management processes, auditors gain access to documented evidence explaining why specific controls were implemented - not just proof that they exist. Updates to risks or policies automatically cascade across all relevant standards, avoiding inconsistencies caused by managing frameworks in silos. Considering that nearly 70% of service organizations now need to demonstrate compliance with at least six frameworks, this alignment is crucial for maintaining defensibility while keeping workloads manageable.
"Real-time control mapping makes evidence a living, current asset - never a last-minute scramble." - ISMS.online
8. Design Policies Based on Risk Priorities
Risk-focused policy design takes the "build once, comply everywhere" concept to the next level. By zeroing in on high-risk areas, you can create tailored policies that address your most pressing vulnerabilities while also meeting multiple compliance standards. Instead of treating all framework requirements equally, focus on what poses the greatest threat. Risk assessments play a key role here, helping you pinpoint high-priority areas and tailor internal measures accordingly. For instance, if privileged account compromises are your top concern, you could implement a unified MFA control that aligns with FedRAMP IA-2, SOC 2 CC6.3, and ISO 27001 A.9.4.2.
Start with a Solid Framework
A strong baseline framework, like NIST 800-53 or ISO 27001 Annex A, provides a modular starting point that covers a wide range of requirements. From there, you can perform gap analyses to identify the "delta" - the remaining requirements that aren't yet addressed - and focus your resources on those high-risk areas. For example, organizations adopting ISO 27001 often find that it satisfies 83% of NIST Cybersecurity Framework requirements and up to 95% of SOC 2 Trust Services Criteria. This approach allows you to directly link controls to risks, creating a robust foundation.
Connect Controls to Risk Registers
A centralized risk register acts as your single source of truth, enabling you to map one risk to multiple frameworks simultaneously. By linking controls directly to identified risks, you create clear and auditable traceability. This integration ensures that controls are implemented as part of your workflows. The benefits are tangible: integrated strategies can reduce compliance costs by 20% to 30% and improve control maturity by 40%.
"A security team that spends 30% less time on compliance mapping has 30% more time for architecture, threat modeling, and the work that actually reduces risk." - Chris Lethaby, Co-founder, Open Security Architecture
Automate High-Priority Areas First
Once you've identified your highest risks, automation becomes your best ally. Start by automating evidence collection for the most critical controls. Link policies to live outputs, such as IAM exports or vulnerability scans, so evidence updates automatically. This "policy-as-code" approach allows compliance rules to be expressed in machine-readable formats, enabling systems to enforce and validate them in real time. The impact is substantial: nearly 70% of service organizations now need to demonstrate compliance with at least six frameworks, and automation ensures you’re not manually gathering the same evidence multiple times.
Comparison Table
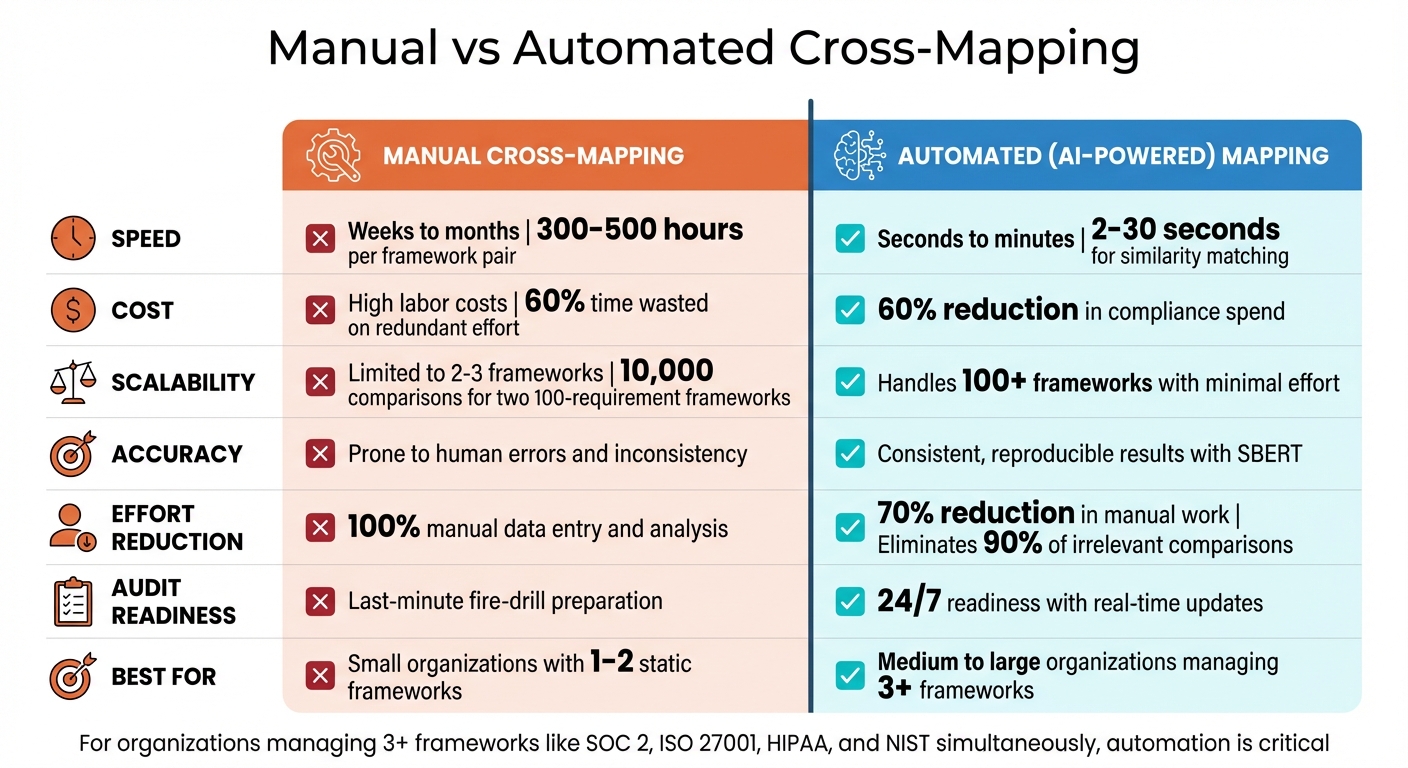
Manual vs Automated Cross-Mapping: Efficiency and Cost Comparison
Choosing between manual and automated cross-mapping isn't just a matter of preference - it directly affects how efficiently your team operates, how scalable your processes are, and how well you can manage compliance costs. The table below highlights the key differences, giving you a clear picture of how each approach impacts your workload, budget, and readiness for audits.
| Factor | Manual Cross-Mapping | Automated (AI-Powered) Mapping |
|---|---|---|
| Speed | Takes weeks to months; requires 300–500 hours per framework pair | Completes in seconds (SBERT) to minutes; similarity matching in 2–30 seconds |
| Cost | High labor costs due to expert involvement; 60% of time wasted on redundant effort | Cuts compliance spend by 60% overall |
| Scalability | Limited; impractical for more than 2–3 frameworks; requires 10,000 comparisons for two 100-requirement frameworks | Highly scalable; handles 100+ frameworks with minimal additional effort |
| Accuracy | Susceptible to errors from human fatigue and inconsistency | Delivers consistent, reproducible results with SBERT |
| Effort Reduction | Fully manual data entry and analysis | Reduces manual work by up to 70%; eliminates 90% of irrelevant comparisons |
| Audit Readiness | Requires last-minute "fire-drill" preparation before audits | Maintains 24/7 readiness with real-time updates |
| Suitability | Best for small organizations managing 1–2 static frameworks | Ideal for medium to large organizations, MSPs with multiple clients, or any group managing 3+ frameworks |
This comparison shows how automation with ISMS Copilot transforms cross-mapping from a slow, error-prone process into something fast and reliable. For companies managing frameworks like SOC 2, ISO 27001, HIPAA, and NIST simultaneously, automation isn't just helpful - it’s critical.
"Leveraging cross-mapping provides another lens to analyze risk... the delta between frameworks can identify a legitimate need for additional controls to combat risk - this is the biggest benefit".
When you're working with three or more frameworks, manual spreadsheets quickly become unmanageable. They lead to "version chaos", where updating one policy doesn’t cascade across other frameworks, creating hidden compliance risks. Tools like ISMS Copilot avoid this by using semantic analysis to understand the intent behind requirements - not just matching keywords. This ensures your control library aligns seamlessly across all certifications, embodying the "build once, comply everywhere" philosophy.
Conclusion
Cross-mapping policies reshapes how organizations handle security governance. By creating a unified control library, identifying shared requirements, and using AI-driven tools like ISMS Copilot, compliance evolves from a tedious, reactive task into a proactive, streamlined process. With this system, updating a single control automatically reflects changes across frameworks like ISO 27001, SOC 2, HIPAA, and others. This approach not only simplifies compliance management but also strengthens your overall security strategy.
Organizations that implement unified mapping reduce compliance efforts by 30%, allowing teams to dedicate more time to addressing real security risks rather than juggling spreadsheets.
"A security team that spends 30% less time on compliance mapping has 30% more time for architecture, threat modeling, and the work that actually reduces risk".
Continuous monitoring eliminates the stress of last-minute audit prep, offering 24/7 readiness instead of scrambling for annual deadlines. A single access report can satisfy multiple audit requirements. When new regulations like the EU AI Act or DORA arise, your existing controls often cover most of the new demands, enabling faster entry into new markets without overhauling your compliance systems. This shift turns compliance into a steady, strategic benefit rather than a recurring headache.
For teams managing three or more frameworks, manual spreadsheets simply can’t keep up. Tools like ISMS Copilot leverage semantic analysis to understand the intent behind requirements, going beyond basic keyword matching. With support for 20+ frameworks and advanced AI cross-mapping, it transforms compliance from a resource drain into a strategic tool for growth.
FAQs
Which framework should I use as my baseline for cross-mapping?
When deciding on a framework, select the one that best aligns with your organization's compliance objectives and integrates well with other standards. Popular choices like ISO 27001, SOC 2, and NIST 800-53 are often recommended. These frameworks are not only widely recognized but also offer flexibility for cross-referencing with multiple other frameworks.
How do I prove one control satisfies multiple frameworks to an auditor?
To demonstrate that a single control satisfies multiple frameworks, you can create a unified control mapping. This approach identifies overlaps between frameworks and builds a reusable library of controls. The goal? To ensure that one well-documented policy addresses similar requirements across different standards, making evidence collection much easier.
For instance, take access management. You could map its requirements across frameworks like NIST 800-53, SOC 2, or FedRAMP. By clearly documenting how the control meets each framework’s standards, you provide auditors with a straightforward, cross-referenced explanation. This not only streamlines compliance but also reduces redundancy in your processes.
What’s the fastest way to keep cross-mapped controls updated as standards change?
The quickest path involves leveraging AI-powered tools to handle tasks such as control mapping, evidence collection, and updating frameworks automatically. Combine this with unified control frameworks to pinpoint overlaps and maintain a centralized control library that aligns with multiple standards at once. This method streamlines processes and keeps things flexible as compliance demands shift over time.
Related Blog Posts
Related Posts

How AI Enhances Multi-Framework Compliance
AI unifies control mapping, automates evidence collection, and provides real-time monitoring to cut audit prep time and reduce compliance errors.

How Real-Time Alerts Reduce ISO 27001 Non-Compliance Risks
Real-time alerts detect threats fast, cut breach costs and audit failures, and keep ISO 27001 logs tamper-proof for continuous compliance.

AI Accuracy in Security: Specialized vs Generic
Specialized AI beats generic models for security compliance—higher accuracy, fewer hallucinations, and audit-ready documentation for ISO 27001 and GRC.
