Multi-Framework Policy Management: Key Practices
Centralize policies, map overlapping controls, and use AI to automate multi-framework compliance, reducing audits and costs.

Multi-Framework Policy Management: Key Practices
Managing compliance with multiple frameworks like SOC 2, ISO 27001, PCI DSS, and GDPR is a growing challenge for organizations. Each framework comes with its own terms, structures, and requirements, leading to inefficiencies and "framework fatigue." By centralizing policies, aligning overlapping controls, and using AI tools, businesses can simplify compliance and reduce workload. Key takeaways:
- Centralized Policy Repositories: Store all policies and evidence in one place for easy access and updates.
- Control Mapping: Identify shared controls and map ISO 27001 to legal requirements to avoid duplication.
- Automation: Use AI tools for ISO 27001 to map, update, and manage policies efficiently.
- Unified Policies: Create "super controls" to satisfy multiple frameworks with a single policy.
These strategies help reduce compliance costs, save time, and minimize errors, while tools like ISMS Copilot streamline workflows and automate repetitive tasks.
::: @figure 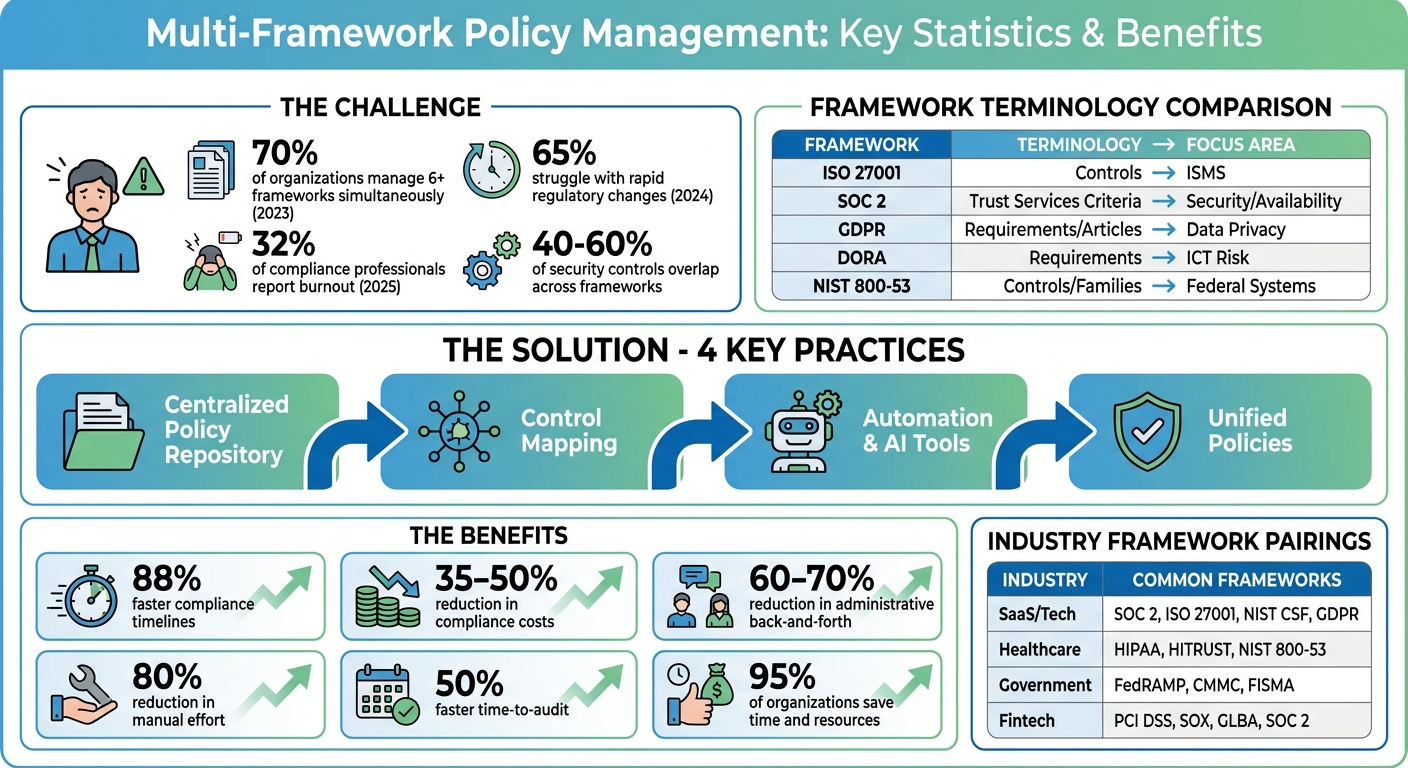 {Multi-Framework Compliance: Key Statistics and Benefits Comparison}
:::
{Multi-Framework Compliance: Key Statistics and Benefits Comparison}
:::
How Platform.sh Cut 900 Controls Using Multi-Framework Harmonization
::: @iframe https://www.youtube.com/embed/j0_6FUVtcuM :::
sbb-itb-4566332
Common Challenges in Multi-Framework Policy Management
Managing policies across multiple frameworks comes with its own set of headaches: inconsistent requirements, overlapping and sometimes conflicting controls, and limited resources to handle the workload. These challenges make compliance a complex puzzle, requiring smarter approaches to keep everything on track. Let’s take a closer look at each issue.
Different Requirements Across Frameworks
Every framework has its own way of doing things - and its own lingo. For example, ISO 27001 uses "controls", SOC 2 focuses on "Trust Services Criteria", and GDPR leans on "requirements" or "articles." Meanwhile, DORA and NIST 800-53 have their own unique structures and terminologies. This isn't just a matter of semantics - it creates real challenges when trying to align frameworks. Direct comparisons become tricky, and manual mapping often leads to errors [1][2].
Switching between frameworks is exhausting for teams. In 2024, 65% of organizations said that keeping up with rapid regulatory changes made it harder to stick to information security best practices [3]. And the workload only grows when managing multiple frameworks. In 2023, nearly 70% of service organizations reported juggling six or more frameworks at once - a daily grind that adds to the mental strain [1][3].
| Framework | Primary Terminology | Key Focus Area |
|---|---|---|
| ISO 27001 | Controls | ISMS |
| SOC 2 | Trust Services Criteria | Security, Availability, Confidentiality |
| GDPR | Requirements / Articles | Data Privacy |
| DORA | Requirements | ICT Risk and Operational Resilience |
| NIST 800-53 | Controls / Families | Federal Information Systems Security |
Overlapping and Conflicting Controls
Frameworks often cover similar ground, but they don’t always align on timing or level of detail. Take breach notification timelines, for instance - each framework has its own deadlines, forcing organizations to default to the strictest one.
Vendor management is another example of overlap. DORA Chapter V, NIS 2 Article 21, and ISO 27001 Annex A.5.19-21 all address supply chain security, but each has unique requirements that need to be carefully mapped [3]. Without proper coordination, organizations risk duplicating efforts. For instance, they might end up creating separate access control policies for SOC 2, ISO 27001, and HIPAA [1][4].
In reality, 40% to 60% of security controls are shared across frameworks. But without proper mapping, these shared controls are often treated as separate tasks, leading to wasted effort [5].
"Managing the overlapping and sometimes conflicting requirements of various frameworks can be daunting, requiring substantial resources and meticulous coordination."
- Emily Bonnie, Senior Content Marketing Manager, Secureframe [1]
Limited Resources
Most organizations don’t have the luxury of big budgets or large compliance teams. Manual evidence collection and constant documentation updates can quickly drain resources. In fact, by 2025, 32% of compliance professionals reported burnout due to increasing workloads [3].
When organizations lack centralized management, they often repeat the same tasks to meet different framework requirements [1][6]. For smaller teams, keeping up with continuous compliance monitoring is a major hurdle [5]. Plus, when IT manages security policies and Legal oversees data privacy, resources aren’t always used efficiently [1].
Some organizations have turned to unified compliance models, cutting manual effort by up to 80% [6]. These models also help reduce compliance costs by 35% to 50% through effective cross-framework mapping [7]. However, implementing these solutions often requires an upfront investment - something that can feel out of reach for resource-strapped teams.
To tackle these challenges, organizations need multi-framework compliance best practices and automation to simplify processes.
Best Practices for Multi-Framework Policy Management
Managing multiple frameworks can feel overwhelming, but centralizing documentation, aligning controls, and streamlining policy updates can make the process smoother. Organizations that excel in this area often implement strategies that cut down on repetitive tasks, minimize errors, and simplify compliance efforts.
Create a Centralized Policy Repository
Say goodbye to scattered documents by consolidating all policies, automated security controls documentation, and procedures into a single, easily accessible location. This "single source of truth" simplifies navigation and reduces time spent searching for critical information.
The most effective repositories use workspaces to keep content organized. For instance, you can create separate workspaces for each framework - ISO 27001, SOC 2, NIST 800-53 - and categorize them by department with clear labels. This approach ensures that data stays organized and prevents overlap while maintaining a central index for quick access [2][8].
To make these repositories even more efficient, include auditor-approved templates and step-by-step instructions. This can cut down on administrative back-and-forth by as much as 60% to 70% [8]. When your team knows exactly where to find the latest access control policy or incident response plan, they can focus on meaningful tasks instead of wasting time hunting for documents.
Another must-have feature is version control. This allows you to track changes, maintain historical data, and assign document owners to streamline reviews [1]. Conduct quarterly reviews to archive completed projects and update active policies as regulations evolve [8].
| Industry Sector | Commonly Paired Frameworks |
|---|---|
| SaaS & Tech | SOC 2, ISO 27001, NIST CSF, GDPR, CCPA, ISO 42001 [1] |
| Healthcare | HIPAA, HITRUST CSF, NIST 800-53 [1][5] |
| Government | FedRAMP, CMMC, FISMA, NIST 800-53, NIST 800-171 [1][5] |
| Fintech/E-commerce | PCI DSS, SOX, GLBA, SOC 2 [1] |
Once your policies are centralized, the next step is to align overlapping controls for maximum efficiency.
Map and Align Controls Across Frameworks
Control mapping is where you can significantly streamline your compliance efforts. By identifying overlaps between frameworks, you can create a unified control library. For example, a single multi-factor authentication (MFA) policy can meet the requirements of FedRAMP, CMMC, and SOC 2 simultaneously [10].
Start by choosing a foundation framework - something comprehensive like NIST 800-53 or ISO 27001 - to serve as your baseline. Then, map other frameworks to it [10].
There are three main approaches to control mapping:
- Semantic mapping: Matches controls with identical objectives, even if the language differs.
- Functional mapping: Aligns controls that achieve similar risk mitigation through different methods.
- Hierarchical mapping: Recognizes when one broad control satisfies multiple specific requirements [7].
For instance, NIST 800-53's AC-2 (Account Management), ISO 27001's A.5.15 (Identity Management), SOC 2's CC6.1 (Logical Access Security), and CMMC's AC.1.001 (Limit system access) all address system access control. When mapping, label relationships as "exact match", "partial overlap", or "no equivalent" to ensure nothing is missed [9]. Also, confirm that evidence requirements align - for instance, SOC 2 might accept screenshots, while FedRAMP demands continuous logs [10].
"Unified control mapping identifies overlaps across frameworks and builds a single control library that satisfies multiple frameworks simultaneously."
- Michael Peters [10]
Done correctly, control mapping can reduce compliance costs by 35% to 50% [7]. Since 60% to 80% of controls often overlap across frameworks, mapping ensures you’re not duplicating efforts. Most organizations discover that 40% to 60% of their security controls are shared across frameworks [5].
Standardize Policy Creation and Updates
Once controls are mapped, standardizing policy creation ensures consistency across the organization. Using uniform templates and processes helps eliminate silos and ensures security practices are applied evenly [3].
Start with auditor-approved templates aligned with major frameworks like ISO, NIST, and SOC 2. Customize these templates to address your specific needs, making sure to reference how each policy ties into the relevant frameworks [3].
Set up automated review cycles to remind policy owners to update documents regularly. This keeps your policies current with regulatory changes and evolving threats. Assign clear document owners and use a centralized GRC platform to manage access and review schedules [1][3].
Consider creating "super controls" that meet the strictest requirements across all frameworks. For example, if one framework calls for annual reviews and another requires quarterly reviews, adopt a quarterly schedule. This approach reduces gaps and ensures compliance with the highest standard [5].
"Address related requirements across multiple frameworks with a single unifying policy or control, streamlining your compliance team's workload and eliminating redundancies."
- Christie Rae, Content Marketing Specialist, ISMS.online [3]
Maintaining a centralized, standardized policy set is far easier than managing fragmented documents across departments [1]. In 2023, 65% of information security professionals reported that keeping up with the rapid pace of regulatory changes was a major challenge [3].
For organizations juggling 50 or more frameworks, tools like ISMS Copilot can simplify the process. This AI-powered compliance assistant offers tailored templates, cross-framework mapping, and policy-writing support for frameworks like ISO 27001, NIS 2, SOC 2, and more. It’s like having a compliance expert on call 24/7, ready to handle the heavy lifting.
Using Technology for Policy Management
Handling policy management across multiple frameworks manually can be exhausting. Once policies are standardized, using advanced technology can significantly improve efficiency and help maintain compliance. Modern tools simplify the process by mapping controls, identifying gaps, and keeping you updated on regulatory changes. By building on centralized repositories and standardized controls, these tools make policy updates and evidence management much smoother.
AI-Powered Policy Mapping and Gap Analysis
While generic AI systems can sometimes produce errors, compliance-specific AI tools are designed to avoid inaccuracies by incorporating verified framework knowledge dynamically. For instance, ISMS Copilot adopted Dynamic Framework Knowledge Injection in February 2025. This advanced system recognizes framework mentions - like ISO 27001 or DORA - and automatically incorporates verified, structured knowledge into its context, ensuring reliable compliance support [13].
As of April 2026, ISMS Copilot supports 17 compliance frameworks, including ISO 27001:2022, SOC 2, GDPR, NIS 2, and DORA [15]. The dynamic injection process typically takes 5 to 15 seconds to retrieve and process relevant framework details during a chat, making it far more efficient than manually cross-referencing standards [12].
To map controls accurately, use specific prompts like: "Map ISO 27001:2022 Annex A.5.15 to SOC 2 CC6.1." Uploading environment details can further tailor policies to your needs [11]. This AI-driven approach can cut policy creation time from weeks to just hours [14].
"AI transforms policy creation from weeks of research and writing into hours of customization and review." - ISMS Copilot Help Center [14]
For gap analysis, the AI evaluates multiple frameworks to pinpoint where your current documentation meets one standard (like ISO 27001) but falls short of others (such as GDPR or DORA). This unified approach allows you to draft policies that satisfy multiple frameworks in a single document, reducing redundancy and ensuring consistency [11].
Automated Workflows and Evidence Management
Automated workflows simplify compliance by generating evidence request lists mapped to specific controls across various frameworks [11][16]. These tools identify documentation gaps ahead of audits, saving you from last-minute scrambles for logs or screenshots.
Workspace isolation is essential for organizations managing multiple clients or business units. Creating separate workspaces - such as "ISO 27001 Certification 2024" or "GDPR Compliance" - helps maintain clear data boundaries and prevents sensitive information from overlapping [2][11]. This is especially useful for consultants or enterprises dealing with diverse regulatory requirements.
Platforms with cross-document consistency checking use AI to spot contradictions or misalignments across policies. For example, if your access control policy states quarterly reviews but a related procedure mentions annual reviews, the system flags the discrepancy [16][17]. It can also detect "orphaned references", such as tasks assigned to vacant roles or procedures linked to non-existent documents, preventing audit issues [16].
Look for tools offering Zero Data Retention (ZDR) agreements to ensure your sensitive data and audit evidence aren’t used to train public AI models [11][13]. For GDPR compliance, choose providers with EU data residency options, such as hosting in Frankfurt, Germany [11]. Security features like mandatory Multi-Factor Authentication (MFA) and end-to-end encryption for data in transit and at rest are also critical [11].
"Your data is NEVER used to train AI models. ZDR agreements ensure your conversations, uploaded documents, and workspace content remain confidential." - ISMS Copilot [13]
Real-Time Monitoring and Reporting
Automated workflows enable continuous compliance oversight through real-time monitoring. These tools can instantly detect threats or audit failures [18]. By automating evidence collection and real-time reporting, you create a single source of truth, avoiding the inefficiencies of managing overlapping controls in separate silos [19].
AI-driven monitoring also tracks regulatory changes, such as updates to DORA or NIS 2, in real time. Using Natural Language Processing (NLP), these systems map changes directly to existing controls, saving you from manually reviewing every update to determine its impact. The system alerts you when a policy needs updating or a new control must be implemented [18].
Organizations using unified compliance tools report a 40% to 60% reduction in compliance costs [19]. They also experience a 50% faster time-to-audit compared to managing frameworks independently [19]. Real-time alerts ensure tamper-proof logs, which are vital for demonstrating continuous compliance during audits [18].
Regularly comparing your Statement of Applicability (SoA) against actual procedures helps confirm that all "applicable" controls are backed by evidence [16]. Creating separate digital workspaces for initial certifications and surveillance audits can track your ISMS maturity over time, showcasing improvement and maintaining compliance [16].
For businesses juggling multiple frameworks, tools like ISMS Copilot offer specialized AI assistance. Pricing starts at $100 per month for the Pro Plan and $250 per month for the Business Plan [11]. These platforms also support analyzing 50 to 500 file uploads per month to verify document consistency, making them suitable for both small teams and larger enterprises [16].
Conclusion
Managing policies across various frameworks doesn't have to overwhelm your team or drain your resources. By combining smart practices with the right technology, you can replace a fragmented, manual process with a system that grows alongside your business. Centralizing your policy repository, mapping controls across frameworks, and streamlining workflows lay the groundwork for technology to enhance your compliance efforts.
Once you establish centralized policies and mapped controls, automated platforms take efficiency to the next level. Organizations using these platforms report compliance timelines that are 88% faster across multiple frameworks, with 95% saving time and resources on certifications [1]. As more companies find themselves juggling six or more frameworks [1][3], the "map once, comply everywhere" strategy becomes a necessity for staying efficient.
Technology also transforms audits from stressful, periodic events into a seamless process of continuous compliance. Automated evidence collection and real-time monitoring ensure you're always ready for an audit, cutting compliance costs by up to 50% and speeding up certification timelines [1]. With 65% of professionals citing regulatory changes as a growing challenge [3], AI tools that track updates and map them to your controls are becoming indispensable.
The benefits aren’t just operational - they’re human too. Automating repetitive tasks like evidence collection and control mapping reduces framework fatigue for your team while improving documentation quality. AI tools can flag inconsistencies before auditors notice them, and unified control libraries eliminate redundant work, making compliance less burdensome.
Starting with a foundational framework like ISO 27001 - which covers 60% to 80% of requirements for other standards - is a smart move [5]. From there, AI-powered mapping can help you close any gaps. Whether you're managing compliance internally or supporting multiple clients, tools like ISMS Copilot are designed to help you navigate over 50 frameworks with ease. Investing in structured practices and intelligent automation pays off through lower costs, quicker certifications, and a compliance program that adapts as your business evolves. These strategies offer a clear path to maintaining compliance while achieving operational success.
FAQs
::: faq
Which framework should we use as our baseline?
Choosing the right baseline framework hinges on your organization’s unique needs, the industry you operate in, and the regulatory requirements you must follow. In the U.S., many organizations opt for ISO 27001 because of its adaptable, risk-focused approach. It also aligns well with other standards like NIST 800-53 and SOC 2, making it easier to build a unified control environment. This reduces redundancy while addressing multiple compliance demands. Always keep your specific compliance objectives in mind when deciding on a framework. :::
::: faq
How do we handle controls that conflict across frameworks?
To handle conflicting controls across various frameworks, it's helpful to use a structured method like control harmonization. This means aligning overlapping controls to comply with the strictest standards across frameworks. Start by analyzing the purpose of each control and adjusting them to fulfill the requirements of multiple frameworks simultaneously.
Using tools like ISMS Copilot can make this process much easier. These tools provide tailored guidance, ready-to-use templates, and features for mapping controls, which not only help maintain compliance but also reduce conflicts and ease the workload for compliance teams. :::
::: faq
What evidence should we standardize for multi-framework audits?
To make multi-framework audits more efficient, focus on standardizing evidence such as control mappings, policies, procedures, and audit artifacts that demonstrate compliance with overlapping standards. By consolidating critical documentation - like risk assessments, incident response plans, and training records - into a single, unified system, you can maintain consistency and avoid unnecessary redundancies.
Building a detailed control inventory can also help align requirements across different frameworks. This approach not only reduces duplication and audit fatigue but also cuts operational costs while ensuring your compliance evidence remains clear and consistent. :::
Related Posts

Best Practices for Cross-Framework Audit Prep
Centralize controls, map overlapping requirements, and automate evidence to reduce audit time and costs across multiple compliance frameworks.

Top 10 GRC Platforms with AI Reporting Features
AI-powered GRC platforms cut manual compliance work with automated evidence, cross-framework mapping, and faster audit reporting.

Unified Control Mapping Across Frameworks: Best Practices
Consolidate overlapping framework requirements into a single control library to cut audit time and centralize evidence.
