Cross-Mapping Frameworks: NIST, ISO 27001, SOC2
Use NIST CSF to build unified controls that map ISO 27001 and SOC 2, reducing audit effort and compliance costs.

Cross-Mapping Frameworks: NIST, ISO 27001, SOC2
Cross-mapping compliance frameworks like NIST CSF, ISO 27001, and SOC 2 can save time, reduce costs, and simplify security management using multi-framework compliance best practices. Instead of handling each framework separately, you can design unified controls that meet overlapping requirements. For example, a single access control process can fulfill SOC 2 CC6.1, ISO 27001 A.5.18, and NIST CSF objectives simultaneously.
Key Takeaways:
- Why cross-mapping matters: 80%–96% of core security controls overlap across these frameworks, reducing duplication.
- Benefits: 30%–50% less effort for evidence collection, 40% lower compliance costs, and improved control consistency.
- How to start:
- Use NIST CSF as a baseline for aligning controls.
- Build a unified control framework (e.g., one policy addressing all frameworks).
- Tag evidence with all applicable requirements upfront.
- Tools to help: AI platforms like ISMS Copilot automate mapping, gap analysis, and document creation.
This approach not only simplifies compliance but also strengthens your overall security program.
::: @figure 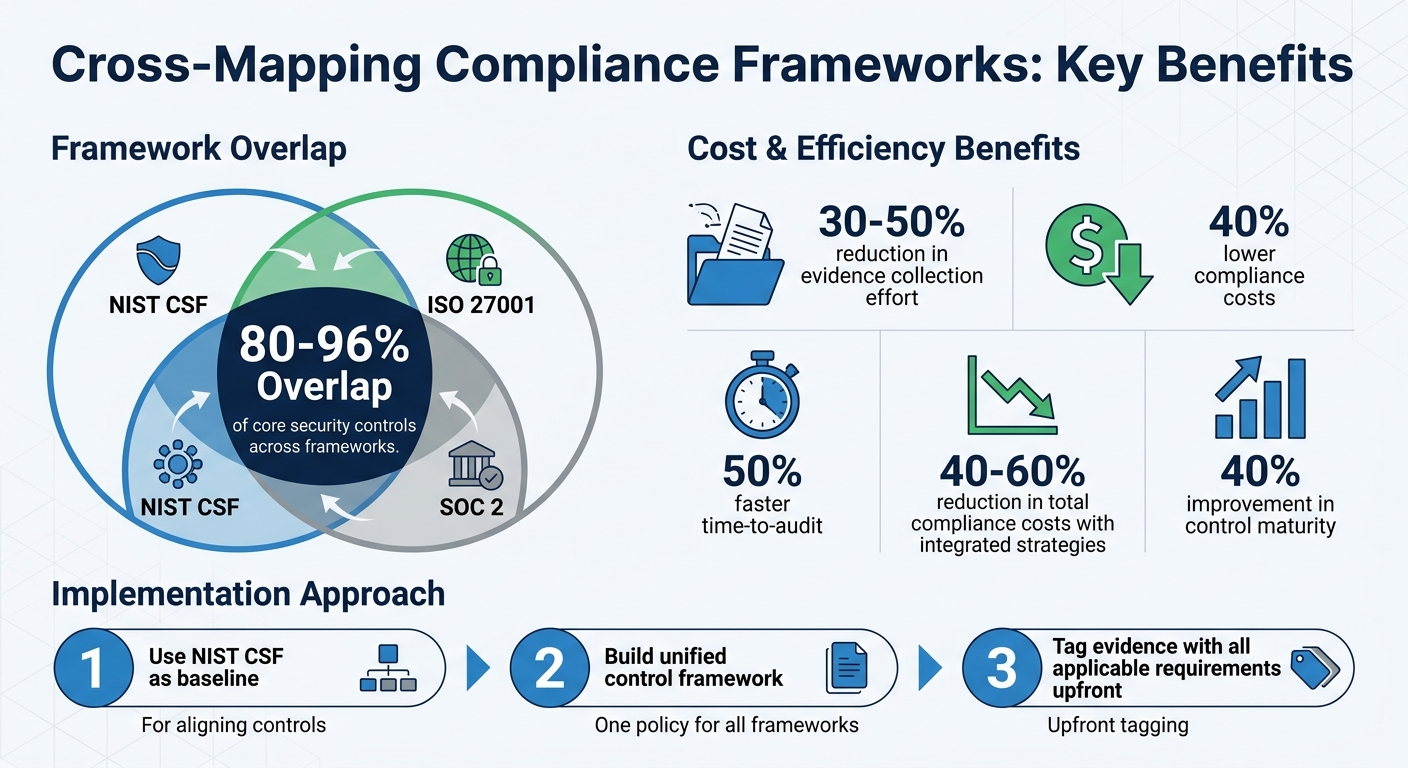 {Cross-Mapping Compliance Frameworks: Benefits and Overlap Statistics}
:::
{Cross-Mapping Compliance Frameworks: Benefits and Overlap Statistics}
:::
Comparing NIST CSF, ISO 27001, and SOC 2: Choosing the Right Cybersecurity Framework
::: @iframe https://www.youtube.com/embed/HiLuSly6krM :::
sbb-itb-4566332
Strategies for Cross-Mapping Frameworks
Managing multiple compliance frameworks can feel overwhelming, but the key lies in strategy. Instead of juggling separate programs, many organizations adopt a Common Control Framework (CCF). This approach allows a single control - like a monthly access review - to address requirements from SOC 2 CC6.1, ISO 27001 A.5.15–A.5.18, and NIST CSF PR.AC all at once , a process that can be streamlined using a cross-framework ISMS assistant [1][6]. By following a "build once, map many" philosophy, businesses cut costs and avoid inconsistencies, creating a more efficient and unified compliance process.
Creating a Unified Control Set
The first step is choosing an anchor framework to serve as your foundation. ISO 27001 Annex A is a strong candidate with its 93 comprehensive controls, while NIST CSF 2.0 works well as a "Rosetta Stone" due to its outcome-based language that can bridge multiple frameworks [1][6]. For example, instead of drafting three separate Access Control Policies, you can create one document that references NIST, ISO, and SOC 2 control numbers in its header [6].
Another crucial step is tagging all evidence with the relevant framework requirements (ISO, SOC 2, NIST) right from the start. This makes audit preparation much simpler, turning it into a quick filtering exercise rather than a last-minute scramble.
Step-by-Step Cross-Mapping Process
Before finalizing controls, take time to define the mappings. Look for overlaps between ISO 27001 Annex A, SOC 2 Trust Services Criteria, and NIST CSF subcategories [6]. Tools like NIST IR 8477 can help classify these relationships as "complete", "partial", or "informational", ensuring no gaps are left uncovered [5].
Conduct a gap analysis to pinpoint unique requirements. For instance, ISO 27001 requires formal management reviews and internal audits, which NIST CSF doesn’t include. Meanwhile, SOC 2 focuses on specific Trust Services Criteria, such as availability and confidentiality, that may need separate attention [5]. By identifying these differences, you can consolidate efforts - for example, by holding one monthly security review to cover control status, risks, and evidence for all frameworks [6].
Using NIST CSF as a Starting Point
NIST CSF can act as a strategic guide for aligning control objectives across frameworks. Its six functions - Govern, Identify, Protect, Detect, Respond, and Recover - offer a strong baseline that connects naturally to other frameworks. For example, the "Govern" function aligns with SOC 2's Common Criteria (CC1-CC3) and ISO 27001's Clauses 4–7, covering organizational context and risk management strategies [1]. This outcome-focused structure bridges the prescriptive nature of ISO 27001 with SOC 2's assurance-driven criteria, highlighting the value of unified frameworks in reducing redundancy.
"The MSPs who thrive... build a common control framework once, map it to everything, and reuse evidence across every audit the client will ever face."
– Oussama Louhaidia, GetCybr [6]
That said, NIST CSF is more about communication and assessment than direct implementation [6]. Use it as your mapping layer, while relying on ISO 27001 for a formal management system and SOC 2 for operational controls. This layered approach combines NIST’s strategic clarity with the operational rigor needed for audit success.
Resources for Cross-Mapping Frameworks
Official Mapping Guides and Documents
The NIST Online Informative References (OLIR) Catalog is a key resource for finding authoritative cross-references. It offers official mappings between frameworks like NIST CSF 2.0, ISO/IEC 27001:2022, and NIST SP 800-53 Rev. 5 [5]. Using its IR 8477 methodology, NIST categorizes these relationships as "complete", "partial", or "informational" [5].
Although NIST does not provide an official mapping between CSF and SOC 2, you can use the AICPA Trust Services Criteria as a foundation [5]. Community-driven tools, such as Razilio, can help bridge this gap. For example, Razilio released an updated NIST CSF 2.0 to ISO 27001:2022 Annexure A mapping in April 2025 that aligns with NIST OLIR standards [7]. For the most accurate results, always begin with official resources like NIST OLIR and then incorporate community tools as needed [5].
Community Tools and Templates
In addition to official guides, community resources can significantly streamline your mapping process. Tools like the Unified Compliance Framework (UCF) offer curated cross-references across numerous compliance standards, while the Cloud Security Alliance (CSA) Cloud Controls Matrix (CCM) focuses on cloud-specific mappings, connecting frameworks like ISO 27001, NIST, and COBIT [8]. These resources can help validate your internal mappings against widely accepted standards.
One effective strategy is to create a unified control matrix. This spreadsheet should list primary controls in rows and corresponding framework requirements in columns [5]. Assign a strength level to each mapping (exact, partial, or none) and include version numbers to ensure you're referencing the latest standards [5]. This method helps prevent redundant work, such as implementing the same control under different names multiple times.
Organizations that adopt integrated mapping strategies often see substantial benefits, including a 40% to 60% reduction in compliance costs and audits completed 50% faster compared to managing frameworks separately [5]. Keep your mapping matrix up to date - review it annually to account for changes like transitioning from NIST CSF 1.1 to 2.0 [5]. Leveraging these tools and strategies allows you to efficiently align and optimize compliance controls across NIST, ISO 27001, and SOC 2 frameworks.
AI Tools for Cross-Mapping
ISMS Copilot for Framework Cross-Mapping
ISMS Copilot takes the unified control strategy to the next level by automating framework cross-mapping with expertise drawn from extensive consulting experience. Unlike general-purpose AI tools that rely on internet searches, ISMS Copilot is built on insights from hundreds of real-world consulting projects. As the platform explains, "Our 'brain' is built from knowledge from hundreds of our own consulting projects. You get practical advice that's been tested in the field" [3].
The tool ensures confidentiality and precision by creating isolated workspaces for specific client-framework combinations, such as "ClientA-ISO27001" or "ClientB-SOC2" [9]. It also allows users to switch between AI personas - like Implementer, Auditor, or Consultant - to get tailored advice for tasks like program development, gap analysis, or strategic guidance [9].
One standout feature of ISMS Copilot is its ability to generate unified control matrices. These matrices map a single implemented control to the requirements of multiple frameworks at once, aligning perfectly with the unified control strategy discussed earlier. Additionally, it automates the creation of framework-specific deliverables, such as Statements of Applicability (SOA) for ISO 27001, System Security Plans (SSP) for NIST, and audit readiness checklists for SOC 2 [5].
The platform also simplifies gap analysis by identifying unique requirements that don’t overlap across frameworks. For instance, ISO 27001 emphasizes formal management reviews, while SOC 2 focuses on managing subservice organizations [5]. It further streamlines framework version updates, such as transitioning from NIST CSF 1.1 to 2.0 or ISO 27001:2013 to 2022, by analyzing changes like deprecated requirements and newly added controls [5][8]. This level of automation not only supports unified control strategies but also makes audit preparation much easier, as detailed in the next section.
How AI-Driven Tools Save Time
AI tools like ISMS Copilot significantly reduce the time and effort required for compliance management. Organizations using these tools report up to a 50% faster time-to-audit when compared to handling frameworks individually [5]. Moreover, unified compliance strategies can cut total compliance costs by 40%–60%, while effective cross-framework mapping reduces evidence collection efforts by 30%–50% for each additional framework added after the first [1].
However, for critical compliance decisions, it’s essential to verify AI-generated mappings against trusted sources like the NIST Online Informative References (OLIR) catalog [9]. This ensures accuracy and alignment with official standards.
How to Implement Cross-Mapping
Implementation Steps
To map compliance requirements across frameworks, start by using the outcome-based structure of NIST CSF or an AI-powered ISMS assistant. Its functions - Identify, Protect, Detect, Respond, Recover, and Govern - are a natural fit for aligning with more detailed standards like ISO 27001 and SOC 2 [1].
Build a unified control matrix where each row lists a primary security control (e.g., "Access Review" or "MFA Configuration"), and columns show how these align with requirements from different frameworks. Add a mapping strength indicator (e.g., exact, partial, none) to highlight how well each control matches [8].
Conduct a gap analysis to find requirements unique to specific frameworks. For instance, ISO 27001 mandates formal ISMS documentation and management review meetings, which aren't explicitly required by NIST CSF. Similarly, SOC 2 includes distinct rules for managing subservice organizations [5]. Keep these unique requirements separate to focus on controls that need special attention.
Streamline evidence collection by tagging each artifact with all relevant framework requirements [1]. This approach allows a single piece of evidence to satisfy multiple auditors, cutting evidence collection efforts by 30% to 50% for every additional framework added after the first [1].
Establish a maintenance schedule to keep your mapping matrix up to date with new framework versions [8]. Review it annually to account for updates such as the transition from NIST CSF 1.1 to 2.0 or ISO 27001:2013 to 2022. Whenever possible, align audit schedules for frameworks like SOC 2 and ISO 27001 to occur around the same time. This way, your team can prepare once and reuse evidence for multiple audits [1].
Once your unified control framework is operational, evaluate its effectiveness using maturity metrics.
Assessing Maturity and Improving Over Time
Use NIST CSF Implementation Tiers as a maturity model to assess how well your framework integration is functioning. These tiers, ranging from Tier 1 (Partial) to Tier 4 (Adaptive), measure how consistently and effectively your security processes operate across all frameworks [5].
Start by developing a "Current Profile" to document which security outcomes you're already achieving across your mapped frameworks. Then, create a "Target Profile" to outline your desired future state. The gap between these two profiles highlights which controls need improvement and which framework requirements still require attention [5].
"The implementation tiers also provide a maturity model that helps organizations assess where they are and where they need to be - across all frameworks simultaneously." - Justin Leapline [1]
Organizations adopting integrated control strategies often see a 40% improvement in control maturity when measured against unified benchmarks [2]. Reassess your Current Profile quarterly to track how many gaps you've closed. Focus on implementing controls that meet three or more framework requirements simultaneously - these deliver the most value for your efforts [5].
As maturity improves, audits become faster and compliance costs drop significantly. Companies with advanced cross-mapping programs report 50% faster time-to-audit compared to those managing frameworks separately, along with a 40% to 60% reduction in overall compliance costs [5].
Conclusion
Cross-mapping frameworks like NIST, ISO 27001, and SOC 2 offers both operational and financial advantages by turning fragmented compliance efforts into a cohesive strategic asset. With an overlap of 80% to 96% in core security controls across these frameworks, organizations can create a single control set that fulfills multiple requirements at once [2]. This "build once, map many" strategy avoids duplicating efforts, reducing compliance costs by as much as 40% to 60% [5].
Leveraging NIST CSF as the common thread ties together the outcome-driven security functions of NIST with the more detailed requirements of ISO 27001 and SOC 2 [1]. For example, a single piece of evidence, like a screenshot of an MFA configuration, can meet the demands of all three frameworks when documentation is unified.
This alignment not only simplifies compliance but also sets the stage for automation. Tools like ISMS Copilot take this a step further by automating tasks such as control mapping, gap analysis, and policy creation. Unlike general-purpose AI tools, ISMS Copilot is tailored specifically for compliance, drawing on practical consulting expertise to produce audit-ready materials while ensuring data privacy with EU-hosted infrastructure [3][4]. Pricing starts at $24/month for individual consultants and scales to $250/month for teams managing multiple projects [3].
Organizations that integrate their control frameworks report 50% faster audit readiness and see a 40% boost in control maturity [2][5]. By centralizing documentation and scheduling, compliance evolves from a reactive task into a proactive security initiative that drives real business value.
FAQs
::: faq
Which framework should I use as the anchor for cross-mapping?
The NIST Cybersecurity Framework (CSF) stands out as an ideal foundation for cross-mapping because its core functions offer a shared language that's easy to understand. It serves as a connector between frameworks like ISO 27001 and SOC 2, simplifying the process of aligning and maintaining consistency across different standards. :::
::: faq
What are the most common gaps between NIST CSF, ISO 27001, and SOC 2?
The differences between NIST CSF, ISO 27001, and SOC 2 come down to their scope, level of detail, and focus areas.
- NIST CSF provides a flexible, high-level framework but doesn't dive into specific, detailed controls.
- ISO 27001 introduces a risk-based approach with rigorous documentation requirements, offering a more structured system.
- SOC 2 focuses on Trust Service Criteria, prioritizing principles like security and availability, though it is less rigid in its requirements.
Because of these variations, organizations often need to map these frameworks carefully to ensure they address all necessary areas. :::
::: faq
How do I reuse evidence across ISO 27001 and SOC 2 audits?
Reusing evidence for ISO 27001 and SOC 2 audits can save a lot of time and effort. The key is to focus on multi-framework control mapping and automated evidence collection.
Start by identifying controls that overlap between the two standards. Once you've pinpointed these, you can test them a single time and use the same evidence for both audits. This approach minimizes duplication and ensures consistency across frameworks.
Using tools like ISMS Copilot can simplify this process. These tools help manage control mappings and organize evidence efficiently, making it easier to meet the requirements of both ISO 27001 and SOC 2 without unnecessary repetition. :::
Related Posts

NIS2 and ISO 27001: Overlap Visualization Guide
Shows how ISO 27001 covers 70–80% of NIS2 and highlights gaps like strict incident reporting and executive accountability.

EU AI Act: Transparency Requirements Explained
Overview of EU AI Act transparency: disclosure rules for chatbots and AI content, documentation standards, timelines, and penalties.

Multi-Framework Policy Management: Key Practices
Centralize policies, map overlapping controls, and use AI to automate multi-framework compliance, reducing audits and costs.
