NIS2 and ISO 27001: Overlap Visualization Guide
Shows how ISO 27001 covers 70–80% of NIS2 and highlights gaps like strict incident reporting and executive accountability.

NIS2 and ISO 27001: Overlap Visualization Guide
Organizations managing critical EU infrastructure or sensitive data often face dual compliance challenges with NIS2 and ISO 27001. The good news? These frameworks overlap by 70–80%, making it possible to align efforts and save 30–40% in compliance costs.
Here’s the key takeaway: If your organization is already ISO 27001:2022 certified, you’ve likely met most of NIS2’s requirements, especially in areas like risk management, incident handling, and business continuity. However, NIS2 introduces stricter demands, such as 24-hour incident reporting and executive accountability, which ISO 27001 doesn’t fully address.
What you’ll learn:
- How NIS2 and ISO 27001 align
- Where gaps exist and how to address them
- Tools and methods (like Venn diagrams, heat maps, and matrices) to visualize overlaps and streamline compliance
Mapping ISO 27001 to NIS2: Strategy for Faster Compliance
::: @iframe https://www.youtube.com/embed/J6fYg2mG_8Q :::
sbb-itb-4566332
Where NIS2 and ISO 27001 Overlap
NIS2 and ISO 27001 share a substantial structural overlap, estimated at 70% to 80% [3][1]. NIS2 Recital 79 even highlights international standards like ISO 27001 as a reference point [1]. Think of ISO 27001 as the framework for managing systems (the "vehicle") and NIS2 as the set of regulatory rules and deadlines (the "rules of the road") [3].
This overlap includes areas such as risk management, leadership, and incident response. By leveraging these commonalities, organizations can streamline their compliance efforts into a single program, potentially cutting operational costs by 30% to 40% [1][6].
Risk Management Alignment
Both frameworks emphasize a structured approach to identifying, assessing, and mitigating security risks, creating a foundation for unified compliance. ISO 27001's Clauses 6.1, 8.2, and 8.3, along with Annex A control 5.1, align with NIS2 Article 21's demand for "appropriate and proportionate" security measures [1]. ISO 27001's risk-based methodology provides the proportionality framework that NIS2 requires.
This alignment supports the creation of a unified risk register. ISO 27001's risk assessment process already addresses NIS2's requirements for identifying threats, analyzing vulnerabilities, and selecting controls. However, organizations need to expand their analysis to include NIS2's "all-hazards" approach, which considers operational disruptions beyond traditional cyber risks [3][5]. This unified approach simplifies governance and visual mapping of risks.
Leadership and Governance Requirements
Both NIS2 Article 20 and ISO 27001 Clause 5 place a strong emphasis on leadership's role in cybersecurity. They require top management to approve security measures, oversee their implementation, and remain accountable for the organization's security posture [1][2]. However, the two frameworks differ slightly in their demands.
NIS2 goes a step further by requiring mandatory cybersecurity training for board members and imposing personal liability on senior management in cases of gross negligence. By contrast, ISO 27001 only mandates general security awareness under Control A.6.3 [1][3]. To align fully with NIS2, organizations should document executive training sessions to meet the specific requirements of Article 20 [1][3].
Incident Response and Business Continuity
When it comes to incident response, both frameworks align operationally. ISO 27001 Annex A controls 5.24 through 5.30 cover incident handling, which corresponds to NIS2 Article 21 requirements [1][2]. Additionally, both frameworks require business continuity planning to ensure uninterrupted operations during disruptions.
However, there is a notable difference in reporting timelines. ISO 27001 includes incident management but doesn't specify deadlines for external reporting. NIS2, on the other hand, enforces a strict three-stage reporting process: an early warning within 24 hours, a detailed notification within 72 hours, and a final report within one month [1][3][7]. To bridge this gap, organizations need to incorporate these specific deadlines into their ISO 27001 incident response playbooks. These overlaps and differences pave the way for a more detailed mapping of controls in the upcoming section.
Mapping NIS2 to ISO 27001 Controls
::: @figure 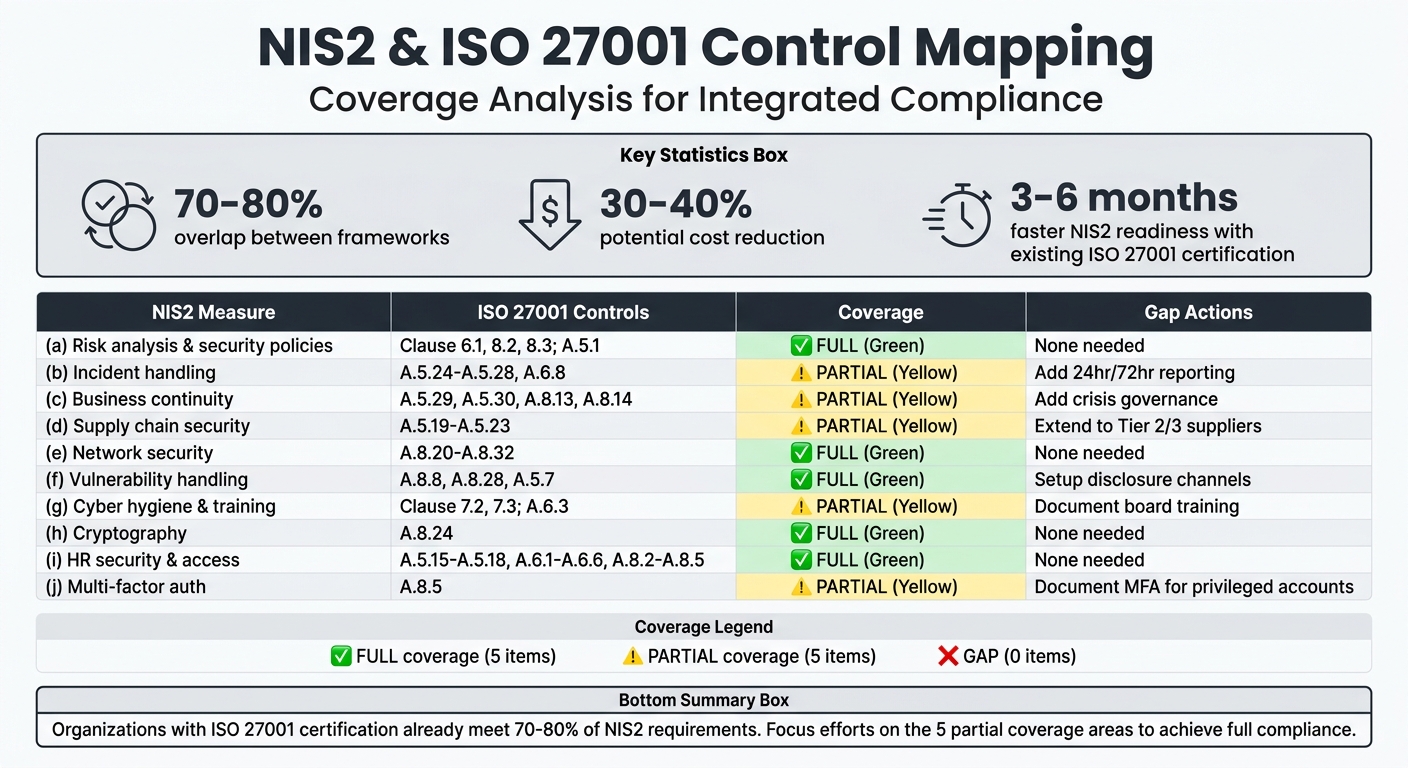 {NIS2 vs ISO 27001 Control Mapping and Coverage Levels}
:::
{NIS2 vs ISO 27001 Control Mapping and Coverage Levels}
:::
Mapping NIS2 requirements to ISO 27001 controls can simplify compliance efforts by highlighting overlaps and identifying gaps, or use an AI-powered assistant to streamline the process. If you already have an Information Security Management System (ISMS) in place, much of the work needed to meet regulatory requirements is likely already done.
To streamline this process, you can enhance your existing Statement of Applicability by adding a column that maps ISO 27001 controls to NIS2 Article 21 measures [1]. This consolidated approach could reduce compliance costs by as much as 30%–40% [1].
"ISO 27001:2022 provides ~70-80% coverage of NIS2 Article 21 requirements." - Saravanan G, Vice President - Cyber Assurance, Glocert [1]
If your organization is already ISO 27001 certified, you could potentially shorten your timeline for NIS2 readiness by 3 to 6 months [1]. The key is to identify where ISO 27001 fully addresses NIS2 requirements and where additional measures are necessary, such as more detailed incident reporting, supply chain evaluations, or executive accountability. This mapping process provides a foundation for better compliance monitoring and visualization.
Control Mapping Table
The table below outlines how NIS2 measures align with ISO 27001 controls, showing areas of full and partial coverage.
| NIS2 Article 21 Measure | ISO 27001:2022 Mapping | Coverage Level | Implementation Notes |
|---|---|---|---|
| (a) Risk analysis & security policies | Clause 6.1, 8.2, 8.3; Control A.5.1 | Full | ISO 27001’s risk methodology aligns with NIS2’s proportionality requirements. |
| (b) Incident handling | Controls A.5.24, A.5.25, A.5.26, A.5.27, A.5.28, A.6.8 | Partial | Update playbooks to include 24-hour early warnings and 72-hour detailed notifications [1]. |
| (c) Business continuity & crisis management | Controls A.5.29, A.5.30, A.8.13, A.8.14 | Partial | Include formal crisis governance structures and communication protocols. |
| (d) Supply chain security | Controls A.5.19, A.5.20, A.5.21, A.5.22, A.5.23 | Partial | Extend assessments to Tier 2/3 suppliers and open-source components [1]. |
| (e) Network & information systems security | Controls A.8.20, A.8.21, A.8.22, A.8.25–A.8.32 | Full | Secure development lifecycle (SDLC) controls align directly. |
| (f) Vulnerability handling & disclosure | Controls A.8.8, A.8.28, A.5.7 | Full | Set up external channels for coordinated vulnerability disclosure. |
| (g) Cyber hygiene & training | Clause 7.2, 7.3; Control A.6.3 | Partial | Document mandatory cybersecurity training for board members as required by Article 20 [1]. |
| (h) Cryptography & encryption | Control A.8.24 | Full | Existing cryptographic controls meet NIS2 standards. |
| (i) HR security & access control | Controls A.5.15–A.5.18, A.6.1–A.6.6, A.8.2–A.8.5 | Full | Personnel screening and access management fully align. |
| (j) Multi-factor authentication (MFA) | Control A.8.5 | Partial | NIS2 requires more detailed documentation of MFA implementation for privileged accounts [1]. |
The areas marked as "Partial" highlight where additional steps are needed to meet NIS2-specific requirements. For example, while ISO 27001 Control A.5.24 covers incident management, it does not enforce the strict 24-hour, 72-hour, or one-month external reporting timelines mandated by NIS2 [1]. Similarly, ISO 27001’s general security awareness training (A.6.3) must be expanded to include documented, mandatory sessions for management to address Article 20’s focus on executive accountability [1].
How to Visualize Control Overlaps
Once you've mapped your controls, the next step is visualizing those overlaps. Visualization tools help clarify gaps, communicate progress, and reduce duplicated efforts. These tools pull your compliance work into a clear, visual framework that’s easier to manage and explain.
The type of visualization you choose depends on your goals. Venn diagrams are great for high-level discussions with executives. Heat maps help pinpoint where your coverage is strong or lacking. And interactive matrices offer a detailed view of control relationships, linking them to evidence and implementation status.
"The ISMS is the vehicle, NIS2 is the rules of the road." - Kopexa [3]
Organizations using integrated visual tools report spending 30-40% less on NIS2 compliance compared to those running separate programs [1].
Venn Diagrams for Framework Overlaps
Venn diagrams are perfect for showing where frameworks like NIS2 and ISO 27001 overlap. For example, ISO 27001:2022 already covers 70-80% of the requirements in NIS2 Article 21 [1][3]. A Venn diagram can highlight these shared areas while pointing out where each standard has unique demands.
The shared section might include risk management (ISO 27001 Clause 6.1 aligning with NIS2 Article 21(a)), cryptography (ISO 27001 Annex A.8.24 aligning with NIS2 Article 21(h)), and access control (ISO 27001 Annex A.5.15–A.5.18 aligning with NIS2 Article 21(i)). On the other hand, NIS2-only areas could include requirements like strict incident reporting, management accountability, and registration with national authorities - elements not directly covered by ISO 27001 [1][8].
This type of diagram is especially helpful in board meetings or stakeholder presentations. It quickly illustrates why ISO 27001 certification alone doesn’t ensure full NIS2 compliance, making it easier to justify additional resources for addressing gaps without overwhelming non-technical audiences.
Heat Maps for Control Coverage
Heat maps use colors to show where your compliance efforts are strong and where they need work. Green typically means full coverage, yellow signals partial coverage, and red highlights gaps.
For example:
- Cryptography and access control might appear green since ISO 27001 Control A.8.24 and Controls A.6.1–A.6.6 align fully with NIS2 [1].
- Incident handling and supply chain security might show yellow because ISO 27001 covers the basics but doesn’t meet NIS2’s stricter requirements, like 72-hour reporting or detailed supplier assessments [1][3].
- Management governance could be red if you haven’t documented the board-level cybersecurity training required by NIS2 Article 20 [1][8].
To create a heat map, expand your Statement of Applicability to include a "Coverage Level" column, labeling each NIS2 measure as "Full", "Partial", or "Gap." Then use conditional formatting in a spreadsheet or GRC tool to apply color-coding. This approach helps security teams focus on the yellow and red zones where changes will have the biggest impact. For deeper analysis, interactive matrices can provide even more detail.
Interactive Matrices for Detailed Mapping
For a more detailed look, interactive matrices link specific NIS2 requirements to ISO 27001 clauses, Annex A controls, and evidence. Unlike static tables, these tools allow users to drill down into details.
Start with an extended Statement of Applicability, adding columns for NIS2 Article 21 references, implementation status, and evidence links. For instance, if you’ve already documented a backup policy for ISO 27001 Control A.8.13, the matrix should also show that this satisfies NIS2 Article 21(c) for business continuity [3]. This creates a single source of truth, eliminating redundant work and ensuring auditors can easily trace compliance across both frameworks.
GRC platforms can automate much of this process, offering real-time updates as controls are completed or new evidence is gathered. Specialized tools like ISMS Copilot One can further streamline these multi-step compliance workflows. These platforms often integrate with ticketing systems, automatically syncing compliance status across frameworks [3][4]. This level of detail is invaluable for audits and demonstrates comprehensive control management for both standards.
Using ISMS Copilot for Overlap Visualization
ISMS Copilot takes your compliance mapping process to a whole new level by automating and simplifying the visualization methods discussed earlier. Managing compliance for frameworks like NIS2 and ISO 27001 becomes far more efficient when you can rely on automation to handle mapping and visualizations. With its AI capabilities, ISMS Copilot generates cross-framework mappings, pinpoints gaps, and produces audit-ready documentation - eliminating the need for manual spreadsheets.
The platform's workspace system allows you to maintain separate contexts for different frameworks. For instance, you could create workspaces like "Client-ISO27001" and "Client-NIS2" and then use AI prompts to map controls between them. This setup enables targeted queries such as, "Show me the overlap between ISO 27001:2022 Annex A.8 and NIS2 requirements", or, "Map ISO 27001 Clause 6.1 to NIS2 Article 21(a)." By keeping data organized and separate, the tool makes the mapping process seamless.
AI-Powered Visualization Tools
ISMS Copilot excels at creating clear, actionable visualizations. It generates mapping tables and matrices that highlight how NIS2 Article 21 measures align with ISO 27001:2022 Annex A controls. For example, you can upload your existing Statement of Applicability or risk assessment, and the tool will quickly identify any gaps. You might discover, for instance, that ISO 27001 Control A.8.24 (cryptography) fully satisfies NIS2 Article 21(h), but your incident response documentation needs updates to meet NIS2's reporting requirements.
The tool also produces risk heat maps in interactive HTML tables with color-coded cells, making it easy to spot strong, partial, or missing areas of coverage. These visualizations can be continuously refined to meet your specific needs, complementing the manual techniques discussed earlier.
Organizations that integrate AI-assisted tools like ISMS Copilot often report a 50–70% reduction in documentation efforts [10]. Hosted in Frankfurt, Germany, ISMS Copilot ensures EU data residency and GDPR compliance. Additionally, it guarantees that uploaded documents are never used to train the AI model [9].
Simplifying Compliance Tasks
ISMS Copilot goes beyond visualizations to automate a range of compliance tasks. It generates extended Statements of Applicability with NIS2-specific columns, incident response playbooks, and third-party risk assessment templates. These outputs are tailored to your organization’s sector and classification under NIS2.
The platform also includes specialized AI personas. Switch to "Auditor" mode for gap assessments or "Consultant" mode for strategic advice. You can even configure custom instructions to ensure every output aligns with your legal obligations - whether your organization is classified as an "Essential" or "Important" entity under NIS2.
"Think of ISMS Copilot as your specialized research assistant for DORA and NIS2 - accelerating understanding, documentation, and control design while you maintain ultimate accountability." - ISMS Copilot Help Center [9]
Pricing starts with a free tier available at chat.ismscopilot.com. Paid plans are offered at $24/month (Plus) and $100/month (Pro), providing unlimited messaging and team collaboration [5].
Conclusion
Main Points
Understanding the overlap between NIS2 and ISO 27001 can simplify compliance efforts and significantly cut costs. Organizations already certified under ISO 27001 typically meet 70–80% of NIS2 requirements[1][6]. While ISO 27001 provides a structured management system, NIS2 introduces specific regulatory demands - like 24-hour reporting deadlines and executive accountability[3].
Using visualization tools like Venn diagrams, heat maps, or interactive matrices can help pinpoint key gaps. These often include tiered incident reporting (e.g., 24 hours, 72 hours, 30 days), executive liability, and more comprehensive supply chain evaluations[3]. Addressing these gaps through an integrated strategy could reduce costs by 30–40% and shorten implementation timelines by up to 60%[1][8]. For instance, a mid-sized financial institution spending $600,000 on separate compliance efforts might save around $240,000 by streamlining their approach[6]. Beyond cost savings, this method minimizes audit fatigue and demonstrates thorough due diligence to regulators.
With these insights, here’s how you can start integrating these controls into your compliance framework.
Next Steps
Begin with a gap analysis by comparing your current Statement of Applicability (SoA) to the ten measures outlined in NIS2 Article 21. Expand your existing SoA by adding NIS2-specific columns to track missing controls[1]. Focus on high-priority areas, such as updating incident management processes to include external reporting chains, formalizing board-level cybersecurity training, and conducting deeper supply chain reviews beyond Tier 1 vendors.
To simplify this process, consider tools like ISMS Copilot. This AI-driven platform can analyze your existing policies, risk assessments, and security documentation to identify gaps. It creates NIS2-aligned incident response playbooks, extended SoAs, and risk heat maps - all while ensuring EU data residency in Frankfurt. Plans start at $24/month for the Plus tier and $100/month for Pro[5]. You can also try their free version at chat.ismscopilot.com to see how automation can transform your compliance efforts.
FAQs
::: faq
If we’re already ISO 27001:2022 certified, what NIS2 gaps still remain?
Even with ISO 27001:2022 certification, there are still areas that need attention to meet NIS2 compliance. These include strict incident reporting timelines, greater supply chain transparency, clear accountability for the management body, and specific regulatory registration obligations. While ISO 27001 addresses roughly 70–80% of the requirements outlined in NIS2 Article 21, these critical components fall outside its coverage. :::
::: faq
What evidence is required to prove compliance with NIS2’s 24-hour and 72-hour incident reporting?
To align with NIS2’s strict 24-hour and 72-hour incident reporting requirements, it’s essential to provide clear and detailed documentation of your incident management process. Here’s what to include:
- Incident Detection Logs: Showcase how and when the incident was identified. Include timestamps to establish the start of your response timeline.
- Assessment Records: Provide a detailed evaluation of the incident, including its scope, impact, and potential risks. This demonstrates your ability to assess incidents promptly and effectively.
- Response Documentation: Highlight the actions taken to mitigate or resolve the issue. Ensure these steps are time-stamped to confirm they align with the required deadlines.
By presenting comprehensive reports with precise timestamps, you can prove your organization’s capability to meet NIS2’s reporting standards while maintaining transparency and accountability. :::
::: faq
What’s the simplest way to visualize NIS2 vs ISO 27001 overlap for leadership?
One effective way to tackle compliance is by using a structured mapping that highlights overlaps and identifies gaps. Since roughly 70% of NIS2 requirements align with ISO 27001, creating a cross-reference table or diagram can make the process much clearer.
For example, you can match NIS2 articles with corresponding ISO 27001 controls to pinpoint areas of coverage and any gaps - like those related to incident reporting or supply chain obligations. This approach not only clarifies your compliance status but also helps leadership focus on strategic priorities. :::
Related Posts

EU AI Act: Transparency Requirements Explained
Overview of EU AI Act transparency: disclosure rules for chatbots and AI content, documentation standards, timelines, and penalties.

Multi-Framework Policy Management: Key Practices
Centralize policies, map overlapping controls, and use AI to automate multi-framework compliance, reducing audits and costs.

ISO 27001 vs SOC2: Key Differences for Startups
Compare ISO 27001 and SOC 2 for startups: scope, validation, costs, timelines, and which to choose for U.S. or international growth.
