ISO 27001 Risk Assessment with AI: Checklist for Startups
Use AI to speed ISO 27001 risk assessments for startups—scope, asset inventory, scoring, control mapping, and continuous monitoring.

ISO 27001 Risk Assessment with AI: Checklist for Startups
Getting ISO 27001 certification is vital for startups aiming to secure enterprise deals. Without it, many large clients won’t even consider your product. However, the process is often expensive, time-consuming, and resource-intensive - taking up to 12 months and costing $50,000–$150,000.
AI tools are changing this landscape by drastically reducing costs and timelines. Startups can now complete risk assessments and achieve certification in as little as 14 days, cutting timelines by 40–60%. AI simplifies tasks like evidence collection, risk scoring, and mapping to ISO 27001:2022 controls, saving both time and effort.
Here’s how you can use AI to conduct an ISO 27001-compliant risk assessment:
- Define ISMS Scope: Focus on systems handling customer data and critical workflows.
- Inventory Assets: Use AI to identify data, software, and services within your scope.
- Identify Threats: Analyze vulnerabilities across areas like cyberattacks, human error, and system failures.
- Assess Risks: Score risks based on likelihood and impact, ensuring consistency.
- Prioritize and Treat Risks: Use AI insights to focus on critical risks and develop treatment plans.
- Monitor Continuously: Automate updates for ongoing compliance.
Tools like ISMS Copilot make this process easier by automating risk identification, control mapping, and documentation, all while keeping costs low with subscription-based pricing. This approach helps startups achieve certification faster and with fewer resources, allowing teams to focus on growth.
Why Startups Should Use AI for ISO 27001 Risk Assessments
Challenges in Traditional Risk Assessment for Startups
Traditional risk assessments can be overwhelming for startups, especially when resources are tight. For a small team of 20–50 employees, completing a manual risk assessment often takes 2–3 weeks of focused effort. For mid-sized organizations (100–500 employees), this timeframe stretches to 4–6 weeks [1]. The bigger issue, though, is the lack of in-house expertise. Startups rarely employ compliance specialists, leaving them to navigate the intricate requirements of ISO 27001 on their own. It’s a tough ask for engineering teams, who excel at building products, not at mapping the 93 Annex A controls to their tech infrastructure.
On top of that, manual data collection adds another layer of complexity. Gathering information involves weeks of interviews with stakeholders and constant documentation updates. This process often leads to inconsistent risk scoring, which could raise red flags during audits. Many companies also rely on generic threat templates instead of tailoring scenarios to their specific setup - like an AWS-hosted PostgreSQL database - which increases the likelihood of audit issues [1].
This is where AI shines, offering a way to streamline the process while minimizing errors and inconsistencies.
Benefits of AI in Risk Assessments
AI tools simplify risk assessments by tackling these pain points head-on. Startups using AI for ISO 27001 implementation typically cut their time-to-certification by 40–60% [5]. Tasks that used to take weeks, such as identifying assets and assigning risk scores, can now be completed in just hours. AI systems analyze network diagrams and architecture documents to classify assets and calculate consistent risk scores (Likelihood × Impact) [1] [3].
Another major advantage is how AI automates the mapping of risks to ISO 27001:2022 controls. It even generates justifications for compliance statements - a task that would otherwise require days of manual cross-referencing.
For startups juggling compliance and rapid growth, AI offers a cost-effective alternative to hiring expensive consultants. Tools like ISMS Copilot translate complex standards into actionable steps tailored to your needs. They can produce detailed risk registers and treatment plans, allowing your team to focus on innovation rather than compliance bottlenecks. And with subscription plans starting at $24/month [6], the financial benefits are hard to ignore compared to traditional consulting fees.
| Feature | Traditional Assessment | AI-Powered Assessment |
|---|---|---|
| Timeframe | Weeks of manual data collection | Hours to generate scenarios |
| Approach | Varies by assessor | Consistent methodology |
| Control Mapping | Manual cross-referencing of 93 controls | Automated mapping and justification |
| Cost Structure | High consulting fees | Subscription-based pricing |
sbb-itb-4566332
ISO/IEC 27001 and ISO/IEC 27005: Managing AI Risks Effectively
::: @iframe https://www.youtube.com/embed/TtnY1vzHzns :::
Preparing for AI-Powered ISO 27001 Risk Assessment
Before diving into AI-driven risk assessments, it's essential to get the groundwork right. ISO 27001 Clause 6.1.2 clearly states that your risk assessment methodology must be documented before identifying risks [1][4][5]. Skipping this step is a serious audit nonconformity [4][5]. Auditors will review whether you followed the correct order, so taking the time to prepare properly is non-negotiable.
AI can simplify this preparation by automating documentation and setup tasks. For example, a startup with 20–50 employees might typically spend 2–3 weeks on the risk assessment phase [1]. With AI-assisted tools, this timeline can be significantly shortened, making the process more efficient. Once your methodology is set, the next steps are defining your ISMS scope and inventorying your assets.
Define the Scope of Your ISMS
The first step is to determine what your Information Security Management System (ISMS) will cover. Prioritize systems that handle customer data, intellectual property, and regulated information [2]. For a SaaS startup, this could include your production database, customer-facing applications, and payment processing systems.
Clearly define organizational boundaries. Specify which teams (e.g., engineering, operations, customer success) and locations (offices, cloud regions like AWS us-east-1, or data centers) fall within the scope [2][9]. If your company operates remotely, document that physical offices are excluded and provide a rationale for auditors [2][8]. ISO 27001 Clause 4.3 mandates this documentation [10].
"Defining scope too broadly will overwhelm resources; too narrow will miss key risks and limit certification value." - ISMS Copilot [5]
Identify all assets supporting critical business processes. For example, if customer onboarding is central to your operations, map out every system and data touchpoint involved in that workflow [1]. Don’t forget to include third-party vendors like Stripe for payments or Auth0 for authentication, as they represent compliance risks [8][11]. Remember, nearly half of all cyber breaches affect businesses with fewer than 1,000 employees [8], and the average cost of a data breach is approximately $4.35 million [8]. Setting a focused scope ensures your AI-powered risk assessment will address the areas that matter most to your startup.
Inventory Assets and Data Flows
Once the scope is defined, the next step is to create a detailed inventory of all assets within your ISMS boundaries. ISO 27001 requires you to identify everything - data, software, physical hardware, cloud services, and individuals with privileged access [1]. Assign ownership and classify each asset as Public, Internal, Confidential, or Restricted [1][4].
AI tools can make this process much faster. For instance, you can upload network diagrams, system architecture documents, or data flow maps, and AI can automatically identify assets and suggest owners [1][12]. You can even prompt AI to generate a tailored asset inventory template specific to your industry, such as fintech or SaaS, ensuring critical examples like PII databases or API integrations are included [1][12].
| Asset Category | Examples for Startups |
|---|---|
| Information Assets | Customer PII, intellectual property, financial records, contracts [1] |
| Software Assets | Databases, SaaS applications, operating systems, security tools [1] |
| Physical Assets | Laptops, servers, mobile devices, network equipment [1] |
| Services | AWS/Azure infrastructure, email services, managed service providers [1] |
| People | Employees, contractors, administrators with privileged access [1] |
Mapping data flows is another critical step. Document how information moves between internal systems and third-party providers to capture every touchpoint [2]. AI can assist by creating process-based maps for sensitive workflows, detailing every system and personnel role involved in handling data [12]. A well-organized and classified asset inventory is the backbone of an effective AI-driven risk assessment.
AI-Driven Checklist for ISO 27001 Risk Assessment
::: @figure 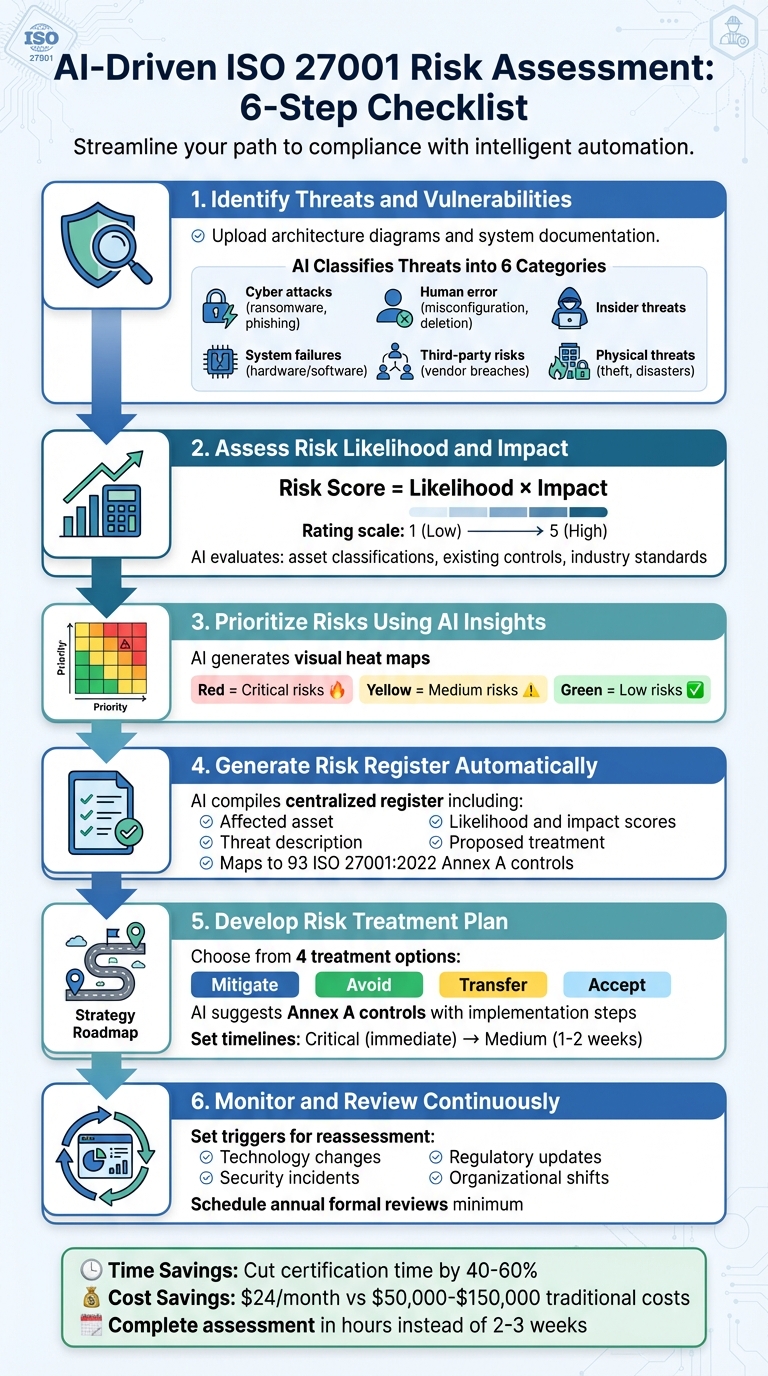 {AI-Powered ISO 27001 Risk Assessment: 6-Step Process for Startups}
:::
{AI-Powered ISO 27001 Risk Assessment: 6-Step Process for Startups}
:::
Using AI can turn the often time-consuming process of manual risk assessments into something faster and more accurate, especially for startups. Once you've defined your scope and inventoried your assets, follow this streamlined checklist to carry out your AI-supported ISO 27001 risk assessment.
Step 1: Identify Threats and Vulnerabilities
Start by uploading architecture diagrams, network maps, or system documentation into your AI tool. Use detailed prompts like, "Identify ISO 27001 threats for a cloud-hosted customer database containing PII" [6].
The AI classifies threats into six main categories: cyber attacks (e.g., ransomware, phishing), human error (like accidental deletion or misconfiguration), insider threats, system failures (hardware or software issues), third-party risks (vendor breaches or service outages), and physical threats (theft or natural disasters) [1][12]. It also detects vulnerabilities specific to your technology, such as unpatched software or weak access controls.
For audit purposes, include prompts like "Show your reasoning" to create a documentation trail. The AI can cross-reference your setup with industry-specific threat trends. For example, ransomware attacks in the healthcare sector have risen by 40% year-over-year [1][12]. Don’t forget to account for human factors like employee training gaps or remote work risks, as well as third-party vendor exposures [12][4].
Step 2: Assess Risk Likelihood and Impact
The AI calculates risk scores using a standard formula:
Risk Score = Likelihood × Impact
Both likelihood and impact are typically rated on a 1–5 scale [1]. The AI evaluates factors like asset classifications, existing controls (e.g., multi-factor authentication, backups, encryption), and industry standards to assign scores [6][4]. For example, a score of 1 might represent a rare or negligible event, while 5 could mean an almost certain or catastrophic outcome [3][4].
| Risk Score Range | Risk Level | Action Required |
|---|---|---|
| 20–25 | Critical | Immediate action; CEO approval needed for delays |
| 15–19 | High | Address within 48 hours; create a treatment plan |
| 8–14 | Medium | Resolve within 1–2 weeks; schedule in the next sprint |
| 1–7 | Low | Monitor and address as needed |
AI can also simulate "what-if" scenarios to show how events like a ransomware attack or vendor failure might affect your overall risk profile. Cross-check these scores with real-world breach data and threat intelligence for accuracy [4].
Once risks are scored, you can move on to prioritizing them.
Step 3: Prioritize Risks Using AI Insights
AI-generated heat maps make it easy to visualize your risk landscape. These maps plot risks by likelihood and impact, using color-coding (e.g., red for critical risks, green for low risks) to highlight what needs immediate attention [3].
For example, an unencrypted production database would likely appear as a high-priority risk, while outdated internal documentation might rank lower. These visual tools help allocate resources to where they’re needed most.
Step 4: Generate a Risk Register Automatically
The AI compiles all identified risks, their scores, and recommended treatments into a centralized risk register. This document should include:
- The affected asset
- Threat description
- Vulnerability exploited
- Likelihood and impact scores
- Overall risk score
- Proposed treatment [1][3]
Keep your risk register in a version-controlled format. The AI can also map relevant ISO 27001:2022 Annex A controls to each risk and suggest implementation steps. The 2022 update reorganized the controls into four themes: Organizational, People, Physical, and Technological, reducing the total from 114 to 93 [5].
A well-maintained risk register ensures you’re ready for audits and helps guide mitigation efforts. Use a dedicated workspace in your AI tool to keep everything organized and separate from other policy drafts. Always review AI-generated scores to ensure they align with your actual security context [6][4].
Step 5: Develop a Risk Treatment Plan
ISO 27001 requires you to choose one of four treatment options for each risk: Mitigate, Avoid, Transfer, or Accept [1][3][4]. The AI suggests treatments based on factors like your risk tolerance, budget, and compliance needs.
For mitigation, the AI might recommend Annex A controls along with implementation steps. For instance, to reduce the risk of unauthorized database access, it could suggest multi-factor authentication, stricter access controls, and encryption. The AI can also draft documentation explaining why certain controls were selected or excluded, which becomes part of your Statement of Applicability (SoA) [1][12][4].
Set practical timelines for each action. Critical risks may require immediate action (with CEO approval for delays), while medium risks could be scheduled for resolution within a week or two [3]. The AI can also help create project plans, assign responsibility, and track progress.
Step 6: Monitor and Review Risks Continuously
Risk assessment isn’t a one-and-done process. ISO 27001 requires ongoing monitoring and periodic reviews to keep your risk register current [12][1]. AI can help by setting triggers for reassessment, such as:
- Technology changes (e.g., new cloud services or system upgrades)
- Security incidents (breaches or near-misses)
- Regulatory updates
- Organizational shifts (like mergers or new product lines) [12][1]
The AI monitors control effectiveness and flags changes in risk scores. For example, if a zero-day vulnerability emerges, the AI recalculates the relevant scores and alerts you. Many organizations report that AI-assisted tools can cut time-to-certification by 40–60% [5].
Schedule formal risk reviews at least annually, or more often in high-risk environments. The AI can generate reports comparing current and past risk levels, highlighting trends and areas that need attention. This creates a continuous improvement loop, ensuring your ISMS stays effective and audit-ready throughout the certification process.
How ISMS Copilot Simplifies Risk Assessments for Startups
ISMS Copilot is designed specifically for information security compliance, offering a focused alternative to general-purpose AI tools like ChatGPT or Claude. It provides ISO 27001 guidance backed by extensive hands-on experience with compliance projects [13].
"Our AI doesn't search the whole internet. It only uses our own library of real-world compliance knowledge. When you ask a question, you get a straight, reliable answer." – ISMS Copilot [13]
The platform ensures data security with dedicated workspaces for audit projects, making it a reliable tool for startups looking to streamline their risk assessment process. Here's how it simplifies each step.
AI-Powered Risk Identification
ISMS Copilot can analyze architecture diagrams, network maps, and system documentation to automatically pinpoint information assets and recommend asset owners [1]. It generates threat scenarios tailored to your technology stack, whether you're using AWS-hosted SaaS solutions or PostgreSQL databases, and aligns these with your industry context [1].
The platform calculates risk scores using the Likelihood × Impact formula on a 1–25 scale, offering clear explanations for each score. This helps meet ISO 27001 Clause 6.1.2 requirements and removes the need for tedious manual cross-referencing.
"Instead of manually cross-referencing 93 Annex A controls, ISMS Copilot instantly identifies relevant controls and explains their applicability to your specific risk scenario." – ISMS Copilot [1]
Multi-Framework Mapping for Compliance
For startups aiming to achieve multiple certifications, ISMS Copilot simplifies the process by mapping risks identified for ISO 27001 to other frameworks like SOC 2 Trust Services Criteria and NIST CSF. It supports over 30 frameworks, including NIS 2, DORA, GDPR, and ISO 42001, ensuring that your compliance efforts remain consistent across various programs without duplicating work [1].
Automated Templates and Reports
ISMS Copilot also takes the hassle out of documentation. It generates structured, audit-ready documents like Risk Registers, Risk Treatment Plans, and Statements of Applicability (SoA) based on your assessment results [1]. For each identified risk, it suggests specific ISO 27001:2022 Annex A controls, explains how they mitigate risks, and outlines the steps for implementation [1].
The platform supports multiple file formats, including PDF, DOCX, and XLS, making it capable of processing even large reports [13]. With this level of automation, small teams (20–50 employees) can complete ISO 27001 risk assessments in just 2–3 weeks - a fraction of the time required for traditional manual methods [1].
Common Pitfalls in Risk Assessments and How AI Solves Them
Startups often stumble on recurring issues during ISO 27001 risk assessments. A frequent problem is relying on generic risk templates that don’t align with the organization’s specific environment. Imagine listing "physical server theft" as a risk when your entire infrastructure is cloud-based - this kind of mismatch can raise eyebrows during audits. ISMS Copilot addresses this by using AI to analyze your technology stack and business model, creating risks that are tailored to your actual setup [1][6].
Another challenge is subjective scoring. Different team members might interpret risks differently, leading to inconsistent ratings. For instance, one person might classify a database vulnerability as "high", while another sees it as "medium." AI eliminates this inconsistency by applying a standardized likelihood and impact methodology across all assessments, ensuring uniformity in how risks are rated [1][3].
Mapping risks to controls is another common pitfall. Startups sometimes choose Annex A controls without clearly documenting which risks those controls mitigate. ISMS Copilot simplifies this by automatically linking each control to its associated risks, explaining the expected risk reduction. This creates a clear and transparent audit trail that aligns with ISO 27001 requirements, making audits smoother [1][7].
Failing to document your risk assessment methodology is also a critical error. ISO 27001 mandates that organizations define their approach before identifying risks. AI tools assist by drafting compliant methodology documents, including detailed guidelines for likelihood and impact scales, ensuring everything is in place before risk identification begins [4][5].
Lastly, overlooking existing security measures can lead to inflated risk scores. For example, assessing inherent risk without considering current protections like firewalls or encryption can distort results. AI evaluates the effectiveness of these existing controls, producing residual risk scores that provide a more accurate picture of your security posture. This approach also supports ongoing risk monitoring, keeping assessments relevant and actionable [4].
Conclusion and Next Steps
Completing an ISO 27001 risk assessment doesn't have to be a drawn-out process. Thanks to AI tools, what used to take small organizations 2-3 weeks can now be done in just a few hours - cutting the time to certification by 40-60% [5]. The secret lies in setting up a solid methodology and leveraging AI to handle tasks like identifying threats, scoring risks, and mapping controls [1][4]. This efficient approach lays the groundwork for effective risk treatment and ensures ongoing compliance.
Once your assessment is done, focus on executing risk treatment plans and updating your Statement of Applicability to validate each Annex A control. Be sure to define clear triggers for reassessments - such as launching a new cloud service, responding to a security incident, or making major infrastructure changes [1][4]. For high and critical risks, consider scheduling bi-weekly reviews to stay ahead of potential threats [3].
ISMS Copilot simplifies this entire process with AI-driven tools for identifying risks and automating control mapping across more than 30 frameworks. The platform offers flexible plans and a free trial, making it easy to get started [6]. Its multi-framework mapping capability allows you to address ISO 27001, SOC 2, and GDPR requirements simultaneously, avoiding duplicate efforts [4][5][6].
To maintain compliance, build on your AI-powered risk register and treatment plans with an adaptable strategy. Establish your risk appetite early, double-check AI-generated scores internally, and schedule regular internal audits - ideally 2-3 months before your certification audit - to catch and address any gaps [14]. With the right AI tools and a well-structured plan, your startup can achieve certification in just 3-4 months, far faster than the usual 6-12 month timeframe [5].
FAQs
::: faq
What evidence will an auditor expect from an AI-assisted risk assessment?
Auditors will require evidence that your risk assessment adhered to a structured and consistent process. This means having clear documentation of how risks were identified, analyzed, and evaluated across critical areas such as security, operations, compliance, and risks unique to AI.
Key pieces of evidence include:
- Risk scores: Quantifying the severity of each identified risk.
- Likelihood and impact assessments: Showing how likely a risk is to occur and the potential consequences.
- Detailed risk treatment plans: Outlining how each risk will be managed or mitigated.
These elements are essential to demonstrate alignment with ISO 27001 standards and ensure your approach is thorough and systematic. :::
::: faq
How do I prove my risk scoring is consistent and not just “AI opinion”?
To keep your risk scoring consistent and free from subjectivity, it’s essential to use a structured, repeatable approach. ISMS Copilot suggests a straightforward five-step process: context review, risk identification, analysis, evaluation, and treatment. By documenting this process and applying it consistently, you can show compliance with ISO 27001. This ensures your risk scores are based on a systematic method and align with established standards, rather than relying on subjective AI-generated outputs. :::
::: faq
What inputs should I provide to AI to avoid generic, non-auditable risks?
To steer clear of generic and non-auditable risks during ISO 27001 risk assessments, it’s crucial to provide detailed, organization-specific inputs. Here’s what to include:
- Industry specifics, company size, and operational details: Tailor the assessment to match your business type and scale.
- ISMS scope: Clearly define the boundaries, including assets and data flow processes.
- Risk assessment methodology: Specify the approach and scoring criteria you use to evaluate risks.
- Threat intelligence and system details: Incorporate data on past incidents, potential threats, and your system’s architecture.
- Stakeholder information and controls: Include details about stakeholders and the controls already in place.
By offering this level of detail, you enable AI to generate results that are precise, actionable, and aligned with ISO 27001 requirements. :::
Related Posts

Unified Control Mapping Across Frameworks: Best Practices
Consolidate overlapping framework requirements into a single control library to cut audit time and centralize evidence.

AI-Powered Compliance Monitoring: How It Works
How ML, NLP, and data integration enable 24/7 compliance monitoring, evidence reuse, risk scoring, and automated remediation.

How Predictive Analytics Simplifies Multi-Framework Compliance
Use AI-driven predictive analytics to map overlapping controls, prioritize risks, and reuse evidence across ISO 27001, SOC 2, and NIS 2.
